 |
 |
| J Navig Port Res > Volume 40(4); 2016 > Article |
ýÜö ýĽŻ
ýÁťŕĚ╝ ýí░ýžüýŁś ýáĽŰ│┤ýťáýÂťýéČŕ│áŕ░Ç ýŚ░ýŁ┤ýľ┤ Ű░ťýâŁÝĽśŰę┤ýäť ýí░ýžüý░ĘýŤÉýŚÉýäť ýáĽŰ│┤Ű│┤ýĽł ŕ┤ÇŰŽČýÖÇ ýáĽŰ│┤Ű│┤ýĽłŰîÇý▒ů ýłśŰŽŻýŁ┤ ýőťŕŞëÝĽśŰőĄ. ÝŐ╣Ý׳ ýí░ýžüŕÁČýä▒ýŤÉŰôĄ ýŁś ýáĽŰ│┤Ű│┤ýĽł ŕ┤ÇŰŽČ ŕ░ĽÝÖö Ű░ęýĽłýŁä ŰžłŰáĘÝĽśŕ│á ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽł ýŁŞýőŁýŁś ýáťŕ│áŰą╝ ýťäÝĽ┤ ŰůŞŰáąýŁä ŕŞ░ýÜŞýŚČýĽ╝ ÝĽťŰőĄ. ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁ┤Ýľë ýáĽŰĆäŕ░Ç ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ Ű»Şý╣śŰŐö ýśüÝľąýŁä ÝÖĽýŁŞÝĽśŕŞ░ ýťäÝĽť ýŚ░ŕÁČ۬ĘÝśĽýŁä ýäĄýáĽÝĽśýśÇýť╝Űę░, ÝĹťŰ│Ş ýžĹŰőĘýť╝Űíť ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžüŕ│╝ ળýťÁ┬ĚŰ│┤ÝŚś ýí░ýžüýŁś ŕÁČýä▒ýŤÉŰôĄýŁä ýäáýἠݼśýśÇŰőĄ. ŕÁČýí░Ű░ęýáĽýőŁ ۬ĘÝśĽýŁä ýŁ┤ýÜęÝĽśýŚČ ŕ▓░ŕ│╝ýÜöýŁŞýŁä ŰĆäýݼśýśÇýť╝Űę░ ýäĄŰČŞýžÇŰą╝ ÝćÁÝĽ┤ ýłśýžĹŰÉť ŰŹ░ýŁ┤Ýä░Űą╝ ýőĄýŽŁýáüýť╝Űíť ŰÂäýäŁÝĽśýśÇŰőĄ. ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžü ŕÁČýä▒ ýŤÉýŁä ŰîÇýâüýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ŰÂäýäŁÝĽť ŕ▓░ŕ│╝ŰŐö ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. ý▓źýžŞ, ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłÝâť ŰĆä, ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰíť ÝÖĽýŁŞŰÉśýŚłýť╝Űę░, ŰĹśýžŞ, ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁŞ ŕ▓âýť╝Űíť ÝÖĽýŁŞŰÉśýŚłŰőĄ. Ű░śŰę┤ýŚÉ ýἠŰ│┤Ű│┤ýĽłý▓śŰ▓îŕ│╝ ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁÇ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ů ýĄÇýłśýŚÉ ýśüÝľąýŁä Ű»Şý╣śýžÇ ýĽŐŰŐö ŕ▓âýť╝Űíť ÝÖĽýŁŞŰÉśýŚłŰőĄ. ýůőýžŞ, ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłś, ýáĽŰ│┤Ű│┤ ýĽłŰŐąŰáą, ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŚÉ ýťáýŁśÝĽť ýśüÝľąýŁä Ű»Şý╣śŰŐö ŕ▓âýť╝Űíť ÝÖĽýŁŞŰÉśýŚłŰőĄ. ŰäĚýžŞ, ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰŐö ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąŕ│╝ ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝Űíť ÝÖĽýŁŞŰÉśýŚłŰőĄ. ŰžłýžÇŰžëýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąŕ│╝ ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŁÇ ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝Űíť ÝÖĽýŁŞŰÉśýŚłŰőĄ.
ABSTRACT
Recently, as cases of organizations' information disclosure occur continuously, it is urgent to manage security of information and establish measures to enhance security of information by an organization itself. Especially, members of an organization should be prepared with measures for information security, and an organization should do its efforts to raise its members' awareness toward information security. I set a research model to verify what effects an organization's fulfillment of regulations to secure information brings to performance of information security and selected members from maritime and port organizations and financial and insurance institutes as sample. Results of the analysis to identify factors affecting information security performance among members of maritime and port organizations are as follows. Firstly, I found that the factors affecting information security awareness are information security attitude and information security standards. Secondly, the factor giving influence on information security policy of an organization was found to be information security standards. In contrast, information security punishments and information security training were verified not to give influence on compliance of information security policy. Thirdly, information security awareness was identified to give significant influence on compliance of information security policy, information security competence and information security behavior. Fourthly, compliance of information security policy was verified to be those factors that give influence on information security competence and information security behavior. Lastly, information security competence and information security behavior were found to be such factors that give influence on information security performance.
ýáĽŰ│┤Ű│┤ýĽłýŁś ý▓┤ŕ│äŰŐö ŰČ╝ŰŽČýáü Ű│┤ýĽł, ŕŞ░ýłáýáü Ű│┤ýĽł, ŕ┤ÇŰŽČýáü Ű│┤ýĽł ýť╝Űíť ŰéśŰłäýľ┤ýžäŰőĄ. ŕŞ░ýŚůŰôĄýŁÇ Ű│┤ýĽłýŁä ýťäÝĽ┤ ýóůýóů ŕŞ░ýłáŕŞ░Ű░śýŁś ýćö ŰúĘýůśŰôĄýŚÉ ÝłČý×ÉÝĽśŕ│á ýŁ┤ýŚÉ ýŁśýí┤ÝĽśýŚČ ýÖöýť╝Űéś ýáĽŰ│┤Ű│┤ýĽłŕ│╝ ŕ┤ÇŰáĘŰÉť ýťäÝŚśŰôĄýŁä ýÂęŰÂäÝ׳ ýáťŕ▒░ÝĽśýžÇ ۬╗ÝľłŰőĄ. ŰČ╝ŰŽČýáü, ŕŞ░ýłáýáü Ű│┤ýĽłŰĆä ýĄĹ ýÜöÝĽśýžÇŰžî ŕ┤ÇŰŽČýáü Ű│┤ýĽłýŁ┤ ŰČ┤ýŚçŰ│┤ŰőĄ ŰŹö ýĄĹýÜöÝĽśŕ▓î ÝĆëŕ░ÇŰÉśýľ┤ýĽ╝ ÝĽś ŰŐö ŰÂÇŰÂäýŁ┤ŰőĄ. ýí░ýžüýŁś ý×Éýé░ýŚÉ ÝĽ┤Űą╝ Űü╝ý╣á ýłś ý׳ŰŐö ýťäÝŚśýÜöýćîýŁŞ Ű│┤ ýĽłýťäÝśĹýŁÇ ýí░ýžüýŁś Űé┤ŰÂÇýáü┬ĚýÖŞŰÂÇýáü ýÜöýŁŞŰôĄýŚÉ ŰîÇÝĽť ŰůŞýÂť, Ű│Çýí░, Ýîîŕ┤┤, ŰÂłŰ▓ĽýéČýÜęýť╝Űíť ýŁŞÝĽ┤ Ű░ťýâŁÝĽťŰőĄ. ۬ůÝÖĽÝĽť ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłŕ┤Ç ŰŽČŰą╝ ýťäÝĽť ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýžÇýőŁ ŕ┤ÇŰáĘ Ű│┤ýĽłŰŐąŰáą Ýľąýâü ŕ│╝ Ű│┤ýĽłÝľëŰĆÖýŁä ŕ░ÇýáŞŰőĄýú╝ŕŞ░ ýťäÝĽ┤ ýÜ░ýäáýáüýť╝Űíť Ű│┤ýĽłýŁŞýőŁýŚÉ ŰîÇÝĽť ýáťŕ│áŕ░Ç ýÜöŕÁČŰÉťŰőĄ(Chen et al., 2008).
ýÜ░ýäá ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ýí░ýžüŕÁČýä▒ýŤÉýŁ┤ Ű░śŰôťýőť ýĄÇýłśÝĽ┤ýĽ╝ ÝĽá ŕ┤ÇŰŽČýáü Ű│┤ýĽłýŁÇ ýí░ýžüýŁś ýáĽŰ│┤ý×Éýé░ ýéČýÜęýŚÉ ŰîÇÝĽť ŰČ┤ýžÇýÖÇ ýőĄýłśŰą╝ ÝĽśýžÇ ýĽŐýĽäýĽ╝ ÝĽśŰę░, ýí░ýžüýáĽŰ│┤ý×Éýé░ýŚÉ ŰîÇÝĽť ŕ┤ÇŰŽČŰą╝ ŰÂÇŰő╣ÝĽť ۬ęýáü ýť╝Űíť ýĽůýÜęÝĽśŰŐö ÝľëŰĆÖýŁä ÝľëÝĽśýžÇ ýĽŐýĽäýĽ╝ ÝĽťŰőĄ. ŰśÉÝĽť ýí░ýžüŕÁČýä▒ýŤÉ ŰôĄýŁ┤ ýí░ýžü ýáĽŰ│┤Ű│┤ýĽł ýťäÝśĹýŚÉ ŰîÇÝĽť ŰÂÇŰÂäýŁä ýćîÝÖÇÝ׳ ŕ┤ÇŰŽČÝĽśŰŐö ŕ▓â ŰĆä ýí░ýžüŰ│┤ýĽłýŚÉ ýőČŕ░üÝĽť Ýö╝ÝĽ┤Űą╝ ŕ░ÇýáŞŰőĄýĄÇŰőĄŰŐö ŕ▓âýŁä ŕ░äŕ│╝ÝĽ┤ýäťŰŐö ýĽł ŰÉťŰőĄ. Űö░ŰŁ╝ýäť ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽ┤ýäťŰŐö ŰČ┤ýŚçŰ│┤ŰőĄ ýí░ýžü ŕÁČýä▒ýŤÉýŁś ýáĽŰ│┤Ű│┤ýĽł ýőĄý▓ťýŁ┤ ŕ░Çý׹ ýĄĹýÜöÝĽť ýÜöŕÁČýéČÝĽşýŁ┤ŰŁ╝ŕ│á Ű│╝ ýłś ý׳ŰőĄ(Siponen, 2000).
ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýŞíýáĽÝĽśŕŞ░ ýťäÝĽť ýäáÝľëýÜöýŁŞýť╝Űíť ŕ░ťýŁŞýáüýŁŞ ý░ĘýŤÉýŁś ÝŐ╣ýä▒ŕ│╝ ýí░ýžüýáüýŁŞ ý░ĘýŤÉýŁś ÝŐ╣ýä▒ ۬ĘŰĹÉŰą╝ ŕ│áŰáĄÝĽ┤ ýáĽŰ│┤Ű│┤ýĽł ýŁ┤ÝľëýŚÉ Űö░ŰąŞ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝Űą╝ ýŞíýáĽÝĽť Űů╝ŰČŞýŁÇ ýŚćýŚłŰőĄ. ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ÝľëÝĽśŰŐö ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁä ýŞíýáĽÝĽĘŕ│╝ ŰĆÖýőťýŚÉ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä ýĄÇýłśÝĽśŰŐö ýí░ýžüýáü ÝŐ╣ ýä▒ýÜöýŁŞýŁä ŕŞ░Ű░śýť╝Űíť ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁ┤ÝľëýŁä ýáĽÝÖĽÝĽśŕ▓î ýŞíýáĽÝĽá ÝĽäýÜöýä▒ýŁ┤ ý׳ŰőĄ(Siponen et al., 2010). ýí░ýžüýŚÉ ýćŹÝĽť ŕ░ťýŁŞýŁś ýἠŰ│┤Ű│┤ýĽłýŁŞýőŁ ýáĽŰĆäýÖÇ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłś ýŚČŰÂÇŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ ýĽł ýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŕ▓î ŰÉťŰőĄ. ÝŐ╣Ý׳ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇ ýłś ýŚČŰÂÇŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝Űą╝ ýťäÝĽť ýžÇý╣ĘýŁ┤ýžÇŰžî ýí░ýžüýŚÉ ýćŹ ÝĽť ŕ░ťýŁŞýŁ┤ ýŁ┤ÝľëÝĽśŰŐö ýáĽŰĆäýŚÉ Űö░ŰŁ╝ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ŕ░Ç ŰőČŰŁ╝ ýžł ŕ▓âýŁ┤ŰőĄ.
Ű│Ş ýŚ░ŕÁČŰŐö ýáĽŰ│┤Ű│┤ýĽł ýŁ┤ÝľëýŁś ŕ┤ÇýáÉýŁä ŕ░ťýŁŞŕ│╝ ýí░ýžüý░ĘýŤÉýŚÉýäť ýŞíýáĽÝĽá ýłś ý׳ŰŐö ýÜöýŁŞýŁä ŰÂäŰąśÝĽśýŚČ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľą ýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ýőĄýŽŁ ŰÂäýäŁÝĽśŰŐö ýŚ░ŕÁČŰíť ŕŞ░ýí┤ ýŚ░ŕÁČýÖÇýŁś ý░ĘŰ│ä ýä▒ýŁä ŰĹÉýŚłŰőĄ. Űö░ŰŁ╝ýäť Ű│Ş ýŚ░ŕÁČýŁś ۬ęýáüýŁÇ ŕ░ťýŁŞýŁś Ű│┤ýĽłýŁŞýőŁýŚÉ ýśü ÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞŕ│╝ ýí░ýžüýŁś Ű│┤ýĽłýáĽý▒ůýĄÇýłśýáĽŰĆäýŚÉ ýśüÝľąýŁä Ű»Şý╣ś ŰŐö ýÜöýŁŞýŁä Ű░öÝâĽýť╝Űíť ýí░ýžüŰ│┤ýĽł ŰŐąŰáą Ýľąýâüŕ│╝ ýáĽŰ│┤Ű│┤ýĽłýŁä ýŁ┤ÝľëÝĽá ýłś ý׳ŰŐö Ű│┤ýĽłÝľëŰĆÖýŁä ýŞíýáĽÝĽśýśÇŰőĄ. ŰśÉÝĽť ýŁ┤ŰčČÝĽť ŰÂäýäŁýŁä ÝćÁÝĽ┤ ýí░ ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ýÁťýóůýáüýť╝Űíť ŰĆäýÂť ÝĽśŕ│áý×É ÝĽťŰőĄ.
ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžü Űé┤ýŁś ýáĽŰ│┤ýŁś ÝŐ╣ýžĽýŁÇ ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. ýÜ░ýäá ýśü ýŚůýáĽŰ│┤ýŁś Ű│┤ýĽłýť╝Űíť ýÜ┤ý×ä, ýćíý׹, ŕ░ÇýĽí, ÝÖöŰČ╝ýáĽŰ│┤ Űô▒ýŁä ŰőĄŰúĘŕ│á ý׳ŰŐö ŰÂÇŰÂäýŚÉýäť ýŚůŰČ┤ýáüýŁŞ ýáĽŰ│┤Ű│┤ýĽłýŁ┤ ýÜöŕÁČŰÉťŰőĄ. ýáäŰ×ÁýáĽŰ│┤ýŁś Ű│┤ ýĽłýť╝ŰíťŰŐö ýí░ýžüýŁś ýśüýŚů ýáäŰ×Á, ÝÖöŰČ╝ Ű│ä ýáäŰ×Á Űô▒ýŁś ýáĽŰ│┤ŕ░Ç ýťáýÂťŰÉś ýžÇ ýĽŐŕ▓î ŕ┤ÇŰŽČÝĽśýŚČýĽ╝ ÝĽťŰőĄ. ŕ░ťýŁŞ Ű░Ć ŕŞ░ýŚůýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽ┤ýäť ŰŐö ýí░ýžüýŁś Űé┤ŰÂÇ ŰŹ░ýŁ┤Ýä░Ű▓áýŁ┤ýŐĄýŁś ýťáýÂťýŚÉ ŰîÇÝĽť Ýö╝ÝĽ┤Űą╝ Ű░ťýâŁýőťÝéĄ ýžÇ ýĽŐŰĆäŰíŁ ýáĽŰ│┤Ű│┤ýĽłýŁ┤ ýÜöŕÁČŰÉťŰőĄŕ│á Ű│╝ ýłś ý׳ŰőĄ.
ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýŚÉýäťýŁś ýŁŞÝä░ŰäĚŰ╣äýŽłŰőłýŐĄýŁś ýéČýÜęýŁ┤ ÝÖĽŰîÇŰÉśŰę┤ýäť ýἠŰ│┤ ýŁśýí┤ýťĘýŁ┤ ýőČÝÖöŰÉśŕ│á ý׳ŰŐö ýâüÝÖęýŁ┤Űę░ ýŁ┤ŰŐö ýáĽŰ│┤ ŰőĘýáłŕ│╝ ŰłäŰŁŻ, ýáĽŰ│┤ ýťáýÂť ýőť ÝĽ┤ýÜ┤┬ĚÝĽşŰžî ýŚůŰČ┤ýŁś ý░ĘýžłýŁ┤ ýáäý▓┤ýáüýŁŞ ýáĽŰ│┤ýőťýŐĄÝůť ýŁä ŰőĄŰúĘŰę░ ýžäÝľëÝĽśŰŐö ýŁŞÝä░ŰäĚŰ╣äýŽłŰőłýŐĄ ŕĚ╝ŕ░äýŚÉ ýťäÝśĹýŁ┤ Ű░ťýâŁÝĽá ýłś ý׳ŰőĄŰŐö ŕ▓âýŁ┤ŰőĄ. ýŁ┤ŰčČÝĽť ýťäÝśĹýŁä ýéČýáäýŚÉ ýí░ý╣śŰą╝ ýĚĘÝĽśŕŞ░ ýťäÝĽť Ű░ę Ű▓Ľýť╝Űíť Ýśäý×ČýŁś ýáĽŰ│┤ÝćÁýőá ýŁŞÝöäŰŁ╝ýŐĄÝŐŞŰčşý▓ś ÝĽśýŚÉýäťŰŐö Ű│┤ýĽłýŁ┤ ýí░ ýžüýŁś ýâŁýí┤ýŁä ýťáýžÇýőťÝéĄŕŞ░ ýťäÝĽť ÝĽäýłś ýí░ŕ▒┤ýŁ┤ŰŁ╝ŰŐö ŕ▓âýŁä ŰžÉÝĽ┤ýĄÇ ŰőĄ. ÝĽ┤ýÜ┤┬ĚÝĽşŰžîŰÂäýĽ╝Űé┤ýŁś ýáĽŰ│┤ŰŐö ÝÖöŰČ╝, ŕŞ░ýŚů, ŕ░ťýŁŞ, ýáĽŰÂÇýŁś ýáĽŰ│┤ ŕ░Ç ýťáŕŞ░ýáüýť╝Űíť ýľŻÝśÇý׳ŰőĄ. ýáĽŰ│┤ Ű│┤ýĽłýŁś ýĚĘýĽŻýä▒ýŁ┤ ýí┤ý×ČÝĽśŕ│á ý׳ ýť╝Űę░, ýŁ╝Ű░ś ŕŞ░ýŚůýŚÉ Ű╣äÝĽśýŚČ ý▓┤ŕ│äýáüýŁŞ Ű│┤ýĽłýáäŰ×ÁýŁ┤ ýŚćŰőĄŰŐö ŕ▓âýŁ┤ ŰőĄ. ŰśÉÝĽť ÝĽ┤ýÜ┤┬ĚÝĽşŰžî ŕ┤ÇŰáĘ ITŕŞ░ýŚůýŁś ŰőĄýľĹýä▒ ŰÂÇýí▒ýť╝Űíť ýŁŞÝĽť ŕŞ░ ýŚůýŁś ýáĽŰ│┤Ű│┤ýĽłŰîÇý▒ůýŁ┤ ýŁ┤ŰúĘýľ┤ýžÇŕ│á ý׳ýžÇ ýĽŐýŁÇ ýőĄýáĽýŁ┤ŰőĄ.
ÝĽ┤ýÜ┤┬ĚÝĽşŰžîŰÂäýĽ╝ýŁś Ű│┤ýĽłýŁä ýťäÝĽť Űé┤ŰÂÇýáüýŁŞ ýáäŰ×Áýť╝Űíť ŕ┤ÇŰŽČýáü Ű│┤ýĽł, ŰČ╝ŰŽČýáü Ű│┤ýĽł, ýőťýŐĄÝůť Ű│┤ýĽłýŁś ŕ┤ÇýáÉýť╝Űíť ŰîÇýŁĹý▒ůýŁä ŰžłŰáĘÝĽ┤ ýĽ╝ ÝĽťŰőĄ. ýÜ░ýäá ŕ┤ÇŰŽČýáü Ű│┤ýĽłŰÂÇŰÂäýŚÉýäťŰŐö ýáĽŰ│┤Ű│┤ÝśŞŰą╝ ýťäÝĽť ýí░ýžü ŕÁČýä▒ýŤÉýŁś Ű│┤ýĽłŕ┤ÇŰŽČ ýłśýĄÇŕ│╝ ŕ┤ÇŰáĘ ýí░ýžüý▓┤ŕ│ä Ű░Ć ŕ┤ÇŰáĘ ŕ│äÝÜŹýŁä ýłś ŰŽŻÝĽ┤ýĽ╝ ÝĽťŰőĄ. ýí░ýžüýŁś Ű│┤ýĽłýŁä ýžÇýŤÉÝĽśŰŐö ýí░ýžüýŁä ŕÁČýä▒ÝĽśŰę░ ýáĽŰ│┤ Ű│┤ÝśŞ ýáĽý▒ůýŁä ýłśŰŽŻÝĽśŕ│á ýŁŞýáüŰ│┤ýĽłýŚÉ ŰîÇÝĽť ÝćÁýáťŕ░Ç ýŁ┤ŰúĘýľ┤ýáŞýĽ╝ ÝĽť ŰőĄ. ŰČ╝ŰŽČýáü Ű│┤ýĽłýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ÝśŞŰą╝ ýťäÝĽť ŰČ╝ŰŽČýáü ÝćÁýáťýłśýĄÇŕ│╝ ŰČ╝ŰŽČýáü Ýö╝ÝĽ┤ýŚÉ ŰîÇŰ╣äÝĽť ýäĄŰ╣äŰą╝ ýłśýÂĽÝĽśýŚČýĽ╝ ÝĽťŰőĄ. ýŁ┤ŰŐö Ű│┤ýĽłýáť ÝĽť ŕÁČýŚşýŁä ŕ┤ÇŰŽČÝĽśŕ▒░Űéś ýáĹŕĚ╝ ÝćÁýáť ŕŞ░ýłáýŁä ýáüýÜęÝĽśýŚČ ŰîÇŰ╣äÝĽá ýłś ý׳ŰőĄ. ýőťýŐĄÝůť Ű│┤ýĽłýť╝ŰíťŰŐö ýáĽŰ│┤ýőťýŐĄÝůť Ű│┤ýĽłýŁä ýťäÝĽť ŕŞ░ýłáýáüýŁŞ ŰîÇý▒ůýŁä ýłśŰŽŻÝĽśŰŐö ŕ▓âýŁ┤ŰőĄ. Ű░▒ýŚů Ű░Ć Ű│ÁŕÁČ ýőťýŐĄÝůťýŁä ýÖäŰ╣äÝĽśŕ│á ŰäĄ ÝŐŞýŤîÝüČ Ű░Ć O/SŰ│┤ýĽł, DB Ű░Ć ýŁĹýÜę SWýáüýÜęŕ│╝ ýőťýŐĄÝůť ýáĹŕĚ╝ ÝćÁýáť ŕ░Ç ýőĄýőťŰÉśýľ┤ýĽ╝ ÝĽťŰőĄ(Kang, 2013). ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýé░ýŚůýŚÉýäťýŁś ýáĽŰ│┤ ŕŞ░ýłáýŁÇ ŰőĄŰąŞ ýé░ýŚů Ű│┤ŰőĄ ýőáýćŹÝĽśŕ▓î ŰĆäý×ůÝĽśŕ│á ý׳ýť╝Űę░, ýáĽŰ│┤ŕŞ░ýłá ýŁś ŰĆäý×ůýť╝Űíť ýé░ýŚůýŁś ÝÜĘýťĘÝÖöŰą╝ ŰőČýä▒ÝĽśŕ│á ý׳ŰőĄ. ÝŐ╣Ý׳, ÝÖöýú╝, ýäá ýéČ Ű░Ć ÝĆČýŤîŰŹö, ýÜ┤ýćíýéČ, ý╗ĘÝůîýŁ┤ŰäłÝä░Ű»ŞŰäÉ ýÜ┤ýśüýéČ, ŕ┤ÇýäŞý▓ş, ŕÁşÝćáÝĽ┤ ýľĹŰÂÇ Űô▒ ŰőĄýľĹÝĽť ýú╝ý▓┤ŕ░Ç ŕ│ÁŕŞëŰžŁýŁä ŕÁČýÂĽÝĽśŕ│á ý׳ŕ│á ýáĽŰ│┤ýŁś ÝŁÉŰŽä ýŁ┤ ŰőĘýáłŰÉá ŕ▓ŻýÜ░ ŕ│ÁŕŞëŰžŁ ýáäý▓┤ýŚÉýäť ýŚůŰČ┤ ŰžłŰ╣äŕ░Ç ýŁ╝ýľ┤Űéá ýłś ý׳ŰŐö ýâüÝÖęýŁ┤ŰőĄ. ýáĽŰ│┤Ű│┤ýĽłýŁś ŕ┤ÇŰŽČŕ░Ç ŰČ┤ýŚçŰ│┤ŰőĄ ýĄĹýÜöÝĽśŰę░ ýőťŕŞëÝĽśŕ▓î ÝĽ┤ ŕ▓░ÝĽ┤ýĽ╝ ŕ│╝ýáťýŁ┤ŕŞ░ ŰĽîŰČŞýŚÉ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ŕ┤ÇŰŽČýáü ýŞíŰę┤ýŚÉýäťýŁś ýŁŞýáüŰ│┤ýĽłýÜöýćîŰą╝ ÝćÁýáťÝĽá ýłś ý׳ŰŐö ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝Űą╝ ýťäÝĽť ÝĽ┤ŕ▓░Ű░ę ýĽłýŁ┤ ŰžłŰáĘŰÉśýľ┤ýĽ╝ ÝĽťŰőĄ.
ýÁťŕĚ╝ ýŚ░ýŁ┤ýľ┤ Ű░ťýâŁÝĽśýŚČ Ýü░ ýéČÝÜîýáü ŰČŞýáťŰíť ŰîÇŰĹÉŰÉśŕ│á ý׳ŰŐö ŕ░ť ýŁŞýáĽŰ│┤ýťáýÂťýéČŕ│áŕ░Ç ÝĽşŰžîŰČ╝Űąś ÝľëýáĽýŚÉýäťŰĆä Ű░ťýâŁÝĽť ŕ░ťýŚ░ýä▒ýŁä ý░Ę ŰőĘýŚÉ ý░ĘŰőĘÝĽá ۬ęýáüýť╝Űíť ýŁŞý▓ťÝĽşŰžîý▓şýŁÇ ýŁŞý▓ťý▓şŕ│╝, ýŁŞý▓ťÝĽşŰžîŕ│ÁýéČ Ű░Ć ýŁŞý▓ťÝĽşŰ│┤ýĽłŕ│ÁýéČ Űô▒ýŁś ýőťýŐĄÝůťýŚÉ ŰîÇÝĽť ŕ░ťýŁŞ ýáĽŰ│┤Ű│┤ÝśŞ ýőĄÝâťŰą╝ ýŁ╝ýáť ýáÉŕ▓ÇÝĽśŕ│á, ÝĽşŰžîý▓ş Űé┤ Ű│┤ýĽłýőťýŐĄÝůťýŁä ýÁťýőá ýőťýŐĄÝůťýť╝Űíť ŕÁÉ ý▓┤ÝĽśŕ│á ýžüýŤÉŰôĄýŚÉŕ▓î ŕ░ťýŁŞýáĽŰ│┤Ű│┤ÝśŞŕÁÉýťíýŁä ýőĄýőťÝĽśŕ│á ý׳ŰőĄ. ŕ░ťýŁŞ ýáĽŰ│┤ŕ░Ç ýťáýÂťŰÉśýžÇ ýĽŐŰĆäŰíŁ ýžÇýćŹýáüýť╝Űíť ýáÉŕ▓ÇÝĽśŕ│á ŕÁÉýťíýŁä ýőĄýőťÝĽ┤ Űéśŕ░ł ŕ│äÝÜŹýŚÉ Űž×ýÂ░ ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŚÉŕ▓î ýáĽŰ│┤Ű│┤ýĽł ŕ░ĽÝÖö ŰîÇý▒ůýŁä Űžł ŰáĘýŁś ýĄĹýÜöýä▒ýŁ┤ ýőťŕŞëÝĽśŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýáĽŰ│┤Ű│┤ýĽł ýŁ┤ýŐłýŚÉ ŰîÇÝĽť ŕ░ťýŁŞýŁś ŕ┤ÇýőČýŁś ýáĽŰĆä Űíť ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ý×Éŕ░ü Ű░Ć ýáĽŰ│┤Ű│┤ýĽłÝÖťŰĆÖýŚÉ ŰîÇÝĽť ŕ┤ÇýőČ ýáĽŰĆä ŰŁ╝ŕ│á ÝĽá ýłś ý׳ŰőĄ(Choi et al., 2008). Siponen(2000)ýŁÇ ýáĽŰ│┤Ű│┤ýĽł ýŁŞýőŁýŁś ýŽŁŕ░ÇŰŐö ýéČýÜęý×ÉýÖÇ ŕ┤ÇŰáĘŰÉť ýőĄýłśŰą╝ ýÁťýćîÝÖö ÝĽá ŕ▓âýŁ┤ŕ│á ýéČ ýÜęý×É ŕ┤ÇýáÉýŁś Ű│┤ýĽł ŕŞ░ýłá Ű░Ć ýáłý░ĘýŁś ÝÜĘýťĘýä▒ýŁä ýÁťŰîÇÝÖö ÝĽá ŕ▓âýŁ┤ŰŁ╝ ŕ│á ýú╝ý׹ݼśýśÇŰőĄ. ýí░ýžü ŕÁČýä▒ýŤÉýŁś ýáĽŰ│┤Ű│┤ýĽł ýĄĹýÜöýä▒ýŚÉ ŰîÇÝĽť ýŁŞýőŁ ýŁ┤ ýáäýáťŰÉśýžÇ ýĽŐýŁÇ ýâüÝâťýŚÉýäť ýáĽŰ│┤Ű│┤ýĽł ŕŞ░ýłá ý×Éý▓┤ŕ░Ç ýí░ýžüýŁś ýἠŰ│┤ý×ÉýŤÉýŁä ÝÜĘŕ│╝ýáüýť╝Űíť Ű│┤ÝśŞÝĽ┤ ýĄä ýłśŰŐö ýŚćŰőĄ. Chen et al. (2008) ýŁÇ Ű│┤ýĽłýŁŞýőŁýŁÇ ýŁŞŕ░äýÜöýćîýŚÉ ÝĆČÝĽĘŰÉśýľ┤ ý׳ýť╝Űę░ ýŁ┤ýáťŰŐö ŕŞ░ýłáýáü Ű│┤ ýĽł ýćöŰúĘýůśŰ┐ÉŰžî ýĽäŰőłŰŁ╝ ýŁŞŕ░äýŁ┤ ýáĽŰ│┤ý×Éýé░ Ű│┤ÝśŞýŁś ýĄĹýÜö ýÜöýćîŰŁ╝ŕ│á ýú╝ý׹ݾłŰőĄ. ýőĄýáťŰíť Ű│┤ýĽłýťäÝśĹýŁÇ ýéČýÜęý×ÉýŁś ýžÇýőŁŕ│╝ ÝľëŰĆÖýŁś ŰÂÇýú╝ýŁś ýÖÇ ŕ▓░ÝĽŹýŚÉ ŕĚŞ ýžüýáĹýáüýŁŞ ýŤÉýŁŞýŁ┤ ý׳ýť╝Ű»ÇŰíť ýśĄŰŐśŰéáýŁś ýáĽŰ│┤Ű│┤ýĽłýŁś ýä▒ŕ│ÁýŚÉ ý׳ýľ┤ Ű│┤ýĽł ýŁŞýžÇŰŐö ŕŞ░ýłáýáü ýÜöýćîŰ│┤ŰőĄ ŰŹö ýĄĹýÜöÝĽá ýłśŰĆä ý׳ ŰőĄŰŐö ŕ▓âýŁ┤ŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýáťŕ│áŰŐö ýí░ýžüýŁś ýáĽŰ│┤ý×Éýé░ýŚÉ ŰîÇÝĽť ýí░ýžü ŕÁČýä▒ýŤÉ ýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä Ű│┤ýĽłýáĽý▒ůýŚÉ Űö░ŰŁ╝ ýáüýáłÝĽť ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýáťŕ│áŰą╝ ýłśÝľëÝĽśýŚČýĽ╝ ÝĽťŰőĄ. ŕ▓░ŕÁş ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýáťŕ│áŰŐö ý×Éýé░, ýáĽý▒ů, ýáĽŰ│┤ Ű│┤ýĽłýŁŞýőŁŕÁÉýťíýŁ┤ ýőĄÝľëŰÉśýľ┤ýĽ╝ ÝĽśŰŐö ŕ▓âýŁ┤ŰőĄ. ýŁ┤ýâü ýé┤ÝÄ┤Ű│Ş ŰžÄýŁÇ ýŚ░ŕÁČýŚÉýäť ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ Ű│┤ýĽłýťäÝśĹýť╝ŰíťŰÂÇÝä░ ýáĽŰ│┤ ýőťýŐĄÝůťýŁä Ű│┤ÝśŞÝĽśŰŐöŰŹ░ ŕ░Çý׹ ýĄĹýÜöÝĽť ýÜöýćîýŁ┤ŕ│á ýí░ýžüýŁś ýáäý▓┤ýáüýŁŞ ýáĽŰ│┤Ű│┤ýĽł ýä▒ŕ│╝ýŚÉ ŰžĄýÜ░ Ýü░ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁ┤ŰŁ╝ŕ│á ýú╝ý׹ݼśŕ│á ý׳ŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉ ŰîÇÝĽť ýäáÝľëýŚ░ŕÁČŰôĄýŁä ýé┤ÝÄ┤Ű│┤Űę┤ ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. Goodhue & Straub (1991)ŰŐö Ű│┤ýĽł ŕ┤ÇýőČ Ű¬ĘÝśĽýŁä ýáťýőťÝĽśŰę░ ýéČýÜę ý×ÉýŁś ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ŕ┤ÇýőČýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞŰôĄýŚÉ ŰîÇÝĽť ýŚ░ŕÁČÝĽśýśÇŰőĄ. ýŁ┤ ýŚ░ŕÁČýŚÉýäť ýáĽŰ│┤ýőťýŐĄÝůťýŚÉ ŰîÇÝĽť ýáüýáĽÝĽť ýłśýĄÇýŁś ŕ┤ÇýőČŕ│╝ ýŁŞýžÇŰĆäŰŐö ÝĽęŰŽČýáüýŁŞ Ű│┤ýĽł ŰîÇý▒ů ýäáýáĽýŁś ýáäýáťýí░ŕ▒┤ýŁ┤ŰŁ╝ŕ│á ŕ░ÇýáĽÝĽśŕ│á ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ŕ┤ÇýőČýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞŰôĄýŚÉ ŰîÇ ÝĽśýŚČ ýŚ░ŕÁČÝĽśýśÇŰőĄ. ýŁ┤ŰôĄýŁÇ ýőĄýŽŁýŚ░ŕÁČŰą╝ ÝćÁÝĽ┤ ýáĽŰ│┤ýőťýŐĄÝůťýŁś ýśĄýÜę ýŚÉ ŰîÇÝĽť ýí░ýžü ŕ┤ÇŰŽČý×ÉýŁś ýŁŞýőŁŕ│╝ ýáĽŰ│┤ ýőťýŐĄÝůťýŁś ýéČýÜęýŚÉ ŰîÇÝĽť ýŁŞ ýőŁ ýáťŕ│áýÖÇ ŕÁÉýťíýŁ┤ ýéČýÜęý×ÉýŁś ýáĽŰ│┤Ű│┤ýĽł ýäťŰ╣äýŐĄýŚÉ Űžîýí▒ýŚÉ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŰŐö ŕ▓░ŕ│╝Űą╝ Ű░ťÝŝݼśýśÇŰőĄ.
Nosworthy(2000)ŰŐö ýáĽŰ│┤Ű│┤ýĽłýŁś ýőĄÝîĘŕ░Ç ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ýŁŞýőŁ Ű»ŞŰ╣ä, ý×ÉýŤÉ ÝĽáŰő╣ŰÂÇýí▒ Ű░Ć ŕÁÉýťí Ű░Ć ÝŤłŰáĘ ŰÂÇýí▒ýŚÉ ŕŞ░ýŁŞÝĽťŰőĄŕ│á ÝĽśýśÇŰőĄ. Űö░ŰŁ╝ýäť ýáĽŰ│┤Ű│┤ýĽłýŁś ýőĄÝîĘŰą╝ Ű░ęýžÇÝĽśŕŞ░ ýťäÝĽ┤ýäťŰŐö ýáĽŰ│┤Ű│┤ ýĽłýŁś ýŁŞýőŁ ýáťŕ│á Ű░Ć ŕÁÉýťí, ÝŤłŰáĘýŁ┤ ÝĽäýÜöÝĽśŰőĄŰŐö ŕ▓âýŁ┤ŰőĄ. Knapp et al.(2005)ýŁÇ ýáĽŰ│┤Ű│┤ýĽł ÝÜĘŕ│╝ýŁŞýžÇýŚÉ ŰîÇÝĽť ŕ░ťýŁŞýĄĹýőČýŁś ýśüÝľąýÜöýŁŞýŁä ŰÂäýäŁÝĽśýŚČ ýÁťŕ│áŕ┤ÇŰŽČý×ÉýŁś ýžÇýžÇ, ýéČýÜęý×ÉýŁś ÝŤłŰáĘ, Ű│┤ÝśŞŰČŞÝÖö, ýáĽý▒ů ŕ┤ÇŰáĘýä▒, ýáĽý▒ůýáü ŕ░Ľýáť Űô▒ýŁ┤ ýŁŞýžÇŰÉť ýáĽŰ│┤Ű│┤ýĽłýŁś ÝÜĘŕ│╝ýä▒ýŚÉ Ű»Şý╣ś ŰŐö ýśüÝľąýŁä ýŽŁŰ¬ůÝĽśýśÇŰőĄ.
Bulgurcu et al.(2010)ýŁÇ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ ý׳ýľ┤ ýáĽŰ│┤Ű│┤ ýĽłýŁŞýőŁŕ│╝ ýžÇŕ░üŰÉť ŕ│ÁýáĽýä▒ýŁś ýŚşÝĽáÔÇÖýŁ┤ŰŁ╝ŰŐö ýőĄýŽŁýŚ░ŕÁČŰą╝ ÝćÁÝĽ┤ýäť ýἠŰ│┤Ű│┤ýĽłýŁŞýőŁŕ│╝ ýžÇŕ░üŰÉť ŕ│ÁýáĽýä▒ýŁ┤ ÝâťŰĆäýŚÉ ýśüÝľąýŁä ýú╝ŰŐö ŕ▓âýŁä Ű░ŁÝśÇ Űé┤ŕ│á ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ŕĚťý╣Öŕ│╝ ŕĚťýáĽýŁä Űö░Űą┤ŕ▓î ÝĽśŰŐöŰŹ░ ýí░ýžüŕÁČýä▒ ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁŕ│╝ ŕ│ÁýáĽýä▒ýŁś ýŚşÝĽáýŁä ýŽŁŰ¬ůÝĽśýśÇŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ŰîÇÝĽť ýŚ░ŕÁČŰą╝ ýé┤ÝÄ┤Ű│┤Űę┤ ýáĽŰ│┤Ű│┤ýĽł ýéČŕ│á Ű░ťý⣠Ű╣łŰĆä Ű░Ć Ýö╝ÝĽ┤ýśłŰ░ęýŚÉ ŰîÇÝĽť ýŚ░ŕÁČŕ░Ç ýú╝Űą╝ ýŁ┤ŰúĘŕ│á ý׳ŰőĄ. ýáĽŰ│┤Ű│┤ýĽł ýä▒ŕ│╝Ű×Ç ýí░ýžüýŁ┤ ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇŰŽČ ÝćÁýáť ŰśÉŰŐö ÝÖťŰĆÖýŁä ÝćÁÝĽ┤ ýľ╗ŕ│áý×É ÝĽśŰŐö ۬ęýáüýť╝Űíť ýáĽŰ│┤Ű│┤ýĽł ýéČŕ│áýŁś ýśłŰ░ę Ű░Ć ýćÉýőĄ Ű░ęýžÇýÖÇ ŕ░ÖýŁÇ ýćî ŕĚ╣ýáü ۬ęýáüýť╝ŰíťŰÂÇÝä░ ŕ▓ŻýčüýÜ░ýťä, ŕ│Áŕ│ÁýŁ┤Ű»ŞýžÇ, ŕ│áŕ░Ł Űžîýí▒ŕ│╝ ŕ░ÖýŁ┤ ýáĽŰ│┤Ű│┤ýĽłŕ│╝ ŕ┤ÇŰáĘŰÉť ýáüŕĚ╣ýáü ۬ęýáüýŁ┤ ý׳ýŁä ýłś ý׳ŰőĄ. Straub & Collins(1990)ýŁś ýŚ░ŕÁČýŚÉýäťŰŐö ŕ┤ÇŰŽČý×Éŕ░Ç ýéČýÜęý×ÉýŚÉŕ▓î ýáĽŰ│┤ýőťýŐĄÝůť ýŁś ýéČýÜęŕ│╝ ŕ┤ÇŰáĘÝĽśýŚČ ÝŚłýÜęŰÉśŰŐö ÝľëýťäýÖÇ ÝŚłýÜęŰÉśýžÇ ýĽŐŰŐö ŰÂÇýáüýáłÝĽť ÝľëýťäýŚÉ ŰîÇÝĽ┤ ýéČýÜęý×ÉŰôĄýŚÉŕ▓î ŕ│ÁýžÇÝĽśŕ│á, ÝŚłýÜęŰÉśýžÇ ýĽŐŰŐö ýáĽŰ│┤ýőťýŐĄ Ýůť ýśĄ┬ĚŰéĘýÜęýŚÉ ŰîÇÝĽ┤ýäťŰŐö Ű▓îý╣ÖýŁä ŰÂÇýŚČÝĽá ŕ▓ŻýÜ░ ýéČŕ│áŰ░ťýâŁýŁś ÝÜč ýłś, ŕŞ░ÝÜîŰ╣äýÜę ýćÉýőĄ Űô▒ýŁ┤ ýÂĽýćîŰÉśŰŐö ŕ▓âýť╝Űíť ÝÖĽýŁŞÝĽśýśÇŰőĄ. ŰśÉÝĽť ýśł Ű░ęýáü Ű│┤ýĽłŰîÇý▒ůŕ│╝ ŕ░ÖýŁÇ ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ÝłČý×ÉŰŐö ý╗┤ÝôĘÝä░ ýśĄŰéĘýÜę ýŚÉ Űö░ŰąŞ ŰžëŰîÇÝĽť ýćÉýőĄýŁä ÝśäýáÇÝĽśŕ▓î ŕ░ÉýćîýőťÝéČ ýłś ý׳ýŁîýŁä ýžÇýáüÝĽś ýśÇŰőĄ.
Sun(2005)ýŁÇ ýáĽŰ│┤ÝÖö ýä▒ŕ│╝ ýŚ░ŕÁČýÖÇ ŕ░ÖýŁ┤ ÝĆČŕ┤äýáüýŁŞ ýőťŕ░üýŚÉýäť ýí░ýžü Űé┤ýÖŞ ýŁ┤ÝĽ┤Űő╣ýéČý×ÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽł Űžîýí▒ŰĆäýÖÇ ŕ░ÖýŁÇ ýŚşŰčë ŕ░ĽÝÖö Űą╝ ÝĆČÝĽĘÝĽśýŚČ ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝Űą╝ ŰĆäýݼśýśÇŰőĄ. ýŚ░ŕÁČŕ▓░ŕ│╝ ýáĽŰ│┤Ű│┤ýĽł ýä▒ŕ│╝Űą╝ ýáĽŰ│┤Ű│┤ýĽł ýéČŕ│á Ű╣łŰĆäŰą╝ ýĄäý×äýť╝ŰíťýŹĘ ýľ╗ŰŐö ýéČŕ│áŰ╣łŰĆä ŕ░Éýćî ýä▒ŕ│╝, ý×Éýé░ýŁś ýćÉýőĄýŁä ýĄäýŁ┤ŰŐö ý×Éýé░ŕ┤ÇŰŽČ ýä▒ŕ│╝, Ű╣äýŽłŰőłýŐĄ ŕŞ░ÝÜî ýćÉ ýőĄ ŕ░ÉýćîŰíť ýľ╗ŰŐö Ű╣äýŽłŰőłýŐĄ ŕŞ░ÝÜîýä▒ŕ│╝, ÝâÇýéČ ŕ▓Żýčü ýőť ýćÉýőĄ ŕ░ÉýćîŰíť ýľ╗ŰŐö ÝâÇýéČŕ▓Żýčü ýä▒ŕ│╝, ýŁ┤Ű»ŞýžÇ ýőĄýÂö ýćÉýőĄ ŕ░ÉýćîŰíť ýľ╗ŰŐö ýŁ┤Ű»ŞýžÇýä▒ ŕ│╝Űą╝ ŰĆäýݼśýśÇŰőĄ. Kim & Ahn(2013)ýŁÇ ýáĽŰ│┤Ű│┤ÝśŞŰČŞÝÖö, ŕĚťŰ▓öýáü ýőáŰůÉ, Ýľëýťä, ŕ░Çý╣śŕ░Ç ýáĽŰ│┤Ű│┤ÝśŞ ŕĚťýἠýťäŰ░ś ÝľëýťäýŚÉ ýľ┤ŰľáÝĽť ýśüÝľąýŁä Ű»Şý╣śŰŐöýžÇ ýőĄýŽŁŰÂäýäŁ ÝĽśýśÇŰőĄ. ýĽäŰůŞŰ»Ş ŕ░ťŰůÉýŁä ÝćáŰîÇŰíť ýí░ýžü Űé┤ýŚÉ ýäť ýáĽŰ│┤Ű│┤ÝśŞ ŕĚťýáĽýŁś ýĄĹýÜöýä▒ýŚÉ ŰîÇÝĽť ýŁŞýőŁ ŕ▓░ÝĽŹŕ│╝ ýáĽŰ│┤Ű│┤ÝśŞ ŕĚť ýáĽýŁś ŕ░Çý╣ś ŕ▓░ýŚČŰą╝ ýáĽŰ│┤Ű│┤ÝśŞ ýĽäŰůŞŰ»ŞÝśäýâüýť╝Űíť ýáĽýŁśÝĽśŕ│á ýŁ┤ Ýśäýâü ýŁ┤ ýľ┤ŰľáÝĽť ýŚşÝĽáýŁä ÝĽśŰŐöýžÇ ýłśÝľëÝĽśýśÇŰőĄ. ýŚ░ŕÁČŕ▓░ŕ│╝ ý×ÉýőáýŁ┤ ýćŹÝĽť ŕŞ░ýŚůýŁ┤ ýáĽŰ│┤Ű│┤ÝśŞ ŕĚťýáĽýŚÉ ŰîÇÝĽť ŕ┤ÇýőČýŁ┤ ŰćĺŰőĄŕ│á ýâŁŕ░üÝĽáýłśŰíŁ ýáĽŰ│┤ Ű│┤ÝśŞ ýĽäŰůŞŰ»ŞýŚÉ ŰîÇÝĽť ýŁŞýőá ýłśýĄÇýŁÇ Űé«ýĽäýíîýť╝Űę░ ýáĽŰ│┤Ű│┤ÝśŞ ŕĚťýáĽýŚÉ ŰîÇÝĽ┤ ýí░ýžüýŤÉýŁ┤ ýťáýÜęÝĽśŰőĄŕ│á ŰŐÉŰü╝ŰŐö ýáĽŰĆäŕ░Ç ŰćĺýŁäýłśŰíŁ ýáĽŰ│┤Ű│┤ÝśŞ ýĽäŰůŞŰ»ŞýŚÉ ŰîÇÝĽť ýŁŞýőŁ ýłśýĄÇýŁÇ Űé«ýĽäýžÇŰŐö ŕ▓âýť╝Űíť ŰéśÝâÇŰéČŰőĄ.
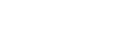
Ű│Ş ýŚ░ŕÁČýŚÉýäťŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞ ŰôĄýŁä ŰÂäýäŁÝĽśŕŞ░ ýťäÝĽśýŚČ ŕ░ťýŁŞýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŞíŰę┤ŕ│╝ ýí░ýžüýŁś ýἠŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłś ŕ┤ÇýáÉýť╝Űíť ŰÂäŰąśÝĽśýśÇýť╝Űę░, ýŁ┤ýŚÉ Űö░ŰąŞ ýí░ýžüýŁś ýἠŰ│┤Ű│┤ýĽł ýŁ┤Ýľëŕ│╝ýŁś ŕ┤ÇŰáĘýä▒ýŚÉ ýé┤ÝÄ┤Ű│┤ŕ│á ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝Űíť ŕÁČýä▒ÝĽśýŚČ ýŚ░ŕÁČ۬ĘÝśĽýŁä ýáťýőťÝĽśýśÇŰőĄ. ýí░ýžüŕÁČýä▒ ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁŕ│╝ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ Űö░ŰąŞ ýí░ ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ýŁ┤ÝľëýŁä ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáą Ű░Ć ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýť╝Űíť ŕÁČ ýä▒ÝĽśýŚČ ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýÖÇýŁś ŕ┤Çŕ│äŰą╝ ýé┤ÝÄ┤Ű│┤ŕ│áý×É ÝĽśýśÇýť╝Űę░, ŰÂäýäŁ ÝĽśŕ│áý×É ÝĽśŰŐö ýŚ░ŕÁČ۬ĘÝśĽýŁÇ ŰőĄýŁîýŁś Fig. 1ŕ│╝ ŕ░ÖŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäýÖÇ ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰą╝ ýäáÝľëýÜöýŁŞýť╝Űíť ŰĆäýݼśýśÇŰőĄ. ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ýŁä ýťäÝĽť ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäŰŐö ýí░ýžüŕÁČýä▒ýŤÉýŁ┤ ýłśÝľëÝĽá ýłś ý׳ŰŐö ýí░ýžüýἠŰ│┤Ű│┤ýĽł ŕ┤ÇŰáĘ ÝÖťŰĆÖ Űô▒ýŚÉ ŰîÇÝĽť ÝśŞýŁśýáüýŁŞ ÝâťŰĆäŰíť Ű│┤ýĽśýť╝Űę░ (Layton, 2005; Workman & Gathegi, 2006), ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäŕ░Ç ÝśĽýä▒ŰÉśýľ┤ ý׳ýŁä ŰĽî ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýťäÝŚśýä▒ýŚÉ ŰîÇÝĽ┤ ŰîÇý▓śÝĽá ýłś ý׳ŰŐö ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁś ýáĽŰĆäŕ░Ç ŰćĺýĽäýžÉýŁä ýäĄŰ¬ůÝĽśŕ│áý×É ÝĽťŰőĄ(Hong et al., 2003). ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰŐö ýí░ýžüýŁś ýáĽŰ│┤ Ű│┤ýĽłÝÖťŰĆÖýŁä ýťäÝĽ┤ Ű│┤ýĽłŕ┤ÇŰáĘ ýéČÝĽşŰôĄýŚÉ ŰîÇÝĽť ŕ┤ÇýőČýáĽŰĆäŰą╝ ýŁśŰ»ŞÝĽś Űę░(Carrie et al., 2004), ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŕ░Ç ŰćĺŰőĄŰę┤ ýí░ýžü ýŁś ýáĽŰ│┤Ű│┤ýĽłýťäÝŚśýä▒ýŚÉ ŰîÇÝĽť Ű│┤ýĽł ŕ┤ÇŰŽČŰîÇý▓śýŚÉ ŕ┤ÇÝĽť ýáĽŰ│┤Ű│┤ýĽłýŁŞ ýőŁýŚÉ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣śŕ▓î ŰÉá ŕ▓âýŁ┤ŰőĄ(Chen et al. 2008). ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰŐö ýáĽŰ│┤Ű│┤ýĽł ŕ┤ÇŰáĘ ýÁťýőáýáĽŰ│┤ýŚÉ ŕ┤ÇýőČýŁ┤ ý׳ŰŐöýžÇ ýŚČŰÂÇýÖÇ ýí░ýžü ýáĽŰ│┤ýőťýŐĄÝůťýŁä ýĽłýáäÝĽśŕ▓î ŕ┤ÇŰŽČÝĽśŕŞ░ ýťäÝĽ┤ ýŐÁŰôŁÝĽ┤ýĽ╝ ÝĽśŰŐö Ű│┤ýĽłŰ░ęŰ▓ĽýŚÉ ŰîÇÝĽť ŕ┤ÇýőČýŁ┤ ŰćĺýĽäý᪠Ű│┤ýĽłÝÖťŰĆÖýŚÉ ýáüŕĚ╣ýáüýť╝Űíť ý░ŞýŚČÝĽśŕŞ░ŰĆä ÝĽťŰőĄ. ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŕ░Ç Űćĺýť╝Űę┤ ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁä ŕ░Çýžł ýłś ý׳ýŁä ŕ▓âýŁ┤ŰőĄ. Űö░ŰŁ╝ýäť ŰőĄýŁîŕ│╝ ŕ░ÖýŁÇ ŕ░Ç ýäĄ1ŕ│╝ ŕ░ÇýäĄ2Űą╝ ŰĆäýݼśýśÇŰőĄ.
[ŕ░ÇýäĄ1] ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäŰŐö ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉ ýἠ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ2] ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰŐö ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉ ýἠ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁÇ ýí░ýžü ŰČŞÝÖöŰą╝ ýל ÝîîýĽůÝĽ┤ ýí░ýžüÝŐ╣ýä▒ýŁä ýŁ┤ÝĽ┤ÝĽś ŕ│á Ű│┤ýĽłýéČÝĽşýŁä Ű░śýśüÝĽśýŚČ ŕĚťŰ▓öýŁ┤ ýל ŕĚťýáĽŰÉśýŚłŰŐöýžÇýŚÉ Űö░ŰŁ╝ ýí░ýžü ýŁś Ű│┤ýĽłýáĽý▒ůýŁä ýĄÇýłś ýŁ┤ÝľëýŚÉ ŰĆäýŤÇýŁ┤ ŰÉá ŕ▓âýŁ┤ŰőĄ(Kang & Chang, 2012). ýáĽŰ│┤Ű│┤ýĽłý▓śŰ▓îýŁ┤ ýí░ýžüýŚÉ ŕĚťýáĽŰÉśýľ┤ ý׳ŰőĄŰę┤ ýí░ýžü ŕÁČýä▒ýŤÉŰôĄýŁÇ ŰÂÇýáĽýáüýŁŞ ýśüÝľąýŁä Ű░ŤŰŐö ŕ▓âýŚÉ ŰîÇÝĽť ŕ▒░ŰÂÇŕ░ÉýŁ┤ Ű░ťýâŁÝĽś ŕŞ░ýŚÉ ýŁ┤Űą╝ ÝÜîÝö╝ÝĽśŕŞ░ ýťäÝĽ┤ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä ýל ýŁ┤ÝľëÝĽśŰŐö ŰŹ░ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣á ŕ▓âýŁ┤ŰőĄ(Lebow & Stein, 1990; Berejikian, 2002). ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁÇ ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŚÉŕ▓î ýáĽŰ│┤Ű│┤ýĽłŕ│╝ ŕ┤ÇŰáĘŰÉť Ű│┤ýĽłÝŐ╣ŕ░ĽýŁ┤Űéś ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŕ┤ÇÝĽť ÝŤłŰáĘýŁä ýőĄ ýőťÝĽśŰŐö ŕ▓âýŁ┤Űę░(Choi et al, 2008), ýí░ýžüýŁÇ ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŚÉ ŰîÇÝĽť ýäŞŰ»ŞŰéśŰą╝ ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŚÉŕ▓î ýáĽŕŞ░ýáüýť╝Űíť ýőĄýőťÝĽśŰŐö ŕ▓âýŁ┤ ýĄĹýÜö ÝĽśŰőĄ(Park, 2012). ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁä ýל ýłśÝľëÝľłŰőĄŰę┤ ýí░ýžüýŁś ýáĽŰ│┤ Ű│┤ýĽłýáĽý▒ůýĄÇýłśýéČÝĽşýŁä Ű░śŰôťýőť Ű░ŤýĽäŰôĄýŚČÝĽśŰę░ ýŁ┤ÝľëÝĽ┤ýĽ╝ ÝĽťŰőĄŰŐö ŕ▓âýŁä ýĽîŕ▓î ŰÉá ŕ▓âýŁ┤ŰőĄ(Nosworthy, 2000). Űö░ŰŁ╝ýäť ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ů ýĄÇýłśýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýäáÝľëýÜöýŁŞýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓ö, ýáĽŰ│┤Ű│┤ýĽł ý▓śŰ▓î, ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíŕ│╝ ŕ┤ÇŰáĘŰÉť ŕ░ÇýäĄ3, ŕ░ÇýäĄ4, ŕ░ÇýäĄ5Űą╝ ŰőĄýŁîŕ│╝ ŕ░ÖýŁ┤ ýłśŰŽŻÝĽśýśÇŰőĄ.
[ŕ░ÇýäĄ3] ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁÇ Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ ýáĽ(+)ýŁś ýśüÝľą ýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ4] ýí░ýžüýŁś Ű│┤ýĽłý▓śŰ▓îýŁÇ Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ ýáĽ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ5] ýí░ýžüýŁś Ű│┤ýĽłŕÁÉýťíýŁÇ Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ ýáĽ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁś ýáĽŰĆäŕ░Ç Űćĺýť╝Űę┤ ýí░ýžüýŁś ýἠŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä ýĄÇýłśÝĽśŰŐö ýáĽŰĆäŕ░Ç ŰćĺýĽäýžł ŕ▓âýŁ┤ŰőĄ(Yim, 2012). ýí░ ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ýéČÝĽşŰôĄýŁä ýל ýĽîŕ│á ý׳ŕŞ░ ŰĽîŰČŞýŚÉ ŕŞ░ýŚůýŁ┤ Ű│┤ýťáÝĽśŕ│á ý׳ŰŐö ý×Éýé░ýáĽŰ│┤Űą╝ ŰőĄýľĹÝĽť ýťäÝśĹýť╝ŰíťŰÂÇÝä░ Ű│┤ÝśŞÝĽśŕ│á ýĄĹ ýÜöÝĽť ýáĽŰ│┤ýťáýÂťýŁ┤ Ű░ťýâŁÝĽśŰŐö ŕ▓âýŁä ýśłŰ░ęÝĽśŕ│áý×É ÝĽá ŕ▓âýŁ┤ŰőĄ(Park & Kim, 2011; Drevin et al., 2007). ýŁ┤ŰŐö ýí░ýžüýŁś ŕ░Çý╣śýÖÇ ýí░ýžü ý×Éýé░ýŚÉ ŰîÇÝĽť ýćÉýőĄŕ│╝ Ýö╝ÝĽ┤Űą╝ ýÁťýćîÝÖöÝĽśŕŞ░ ýťäÝĽť ýí░ýžüýŁś ýžÇý╣Ęŕ│╝ ŕ░ÇýŁ┤ŰôťŰŁ╝ýŁŞýť╝Űíť ŕĚťýáĽŰÉśýľ┤ ý׳ŰŐö ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰíť ÝÖĽýŁŞÝĽá ýłś ý׳ŰőĄ(Bulgurcu et al., 2010). Űö░ŰŁ╝ýäť ýí░ýžüŕÁČýä▒ýŤÉýŁś ýáĽŰ│┤Ű│┤ ýĽłýŁŞýőŁýŁÇ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŕ│á ŕ░Ç ýäĄ6ýŁä ŰĆäýݼśýśÇŰőĄ.
[ŕ░ÇýäĄ6] ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ Ű│┤ýĽłýáĽý▒ů ýĄÇýłśýŚÉ ýἠ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýí░ýžüýŁś ýáĽŰ│┤ý×Éýé░ýŚÉ ŕ░ÇÝĽ┤ýžł ýáĽŰ│┤Ű│┤ýĽł ýťäÝśĹýŁä ýŁŞýőŁÝĽśŰŐö ŕ▓âýŁÇ ýí░ýžü ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ýĚĘýĽŻýä▒ ŕ│╝ ýáĽŰ│┤Ű│┤ýĽł ýőťýŐĄÝůť ŕ┤ÇŰŽČŰą╝ ÝĽá ýłś ý׳ŰŐö ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŁś ýáĽŰĆä ŕ░Ç ŰćĺýĽäýžäŰőĄŰŐö ŕ▓âýŁ┤ŰőĄ(Woo, 2012; Nance & Straul, 2008). ýἠŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽł ýéČÝĽşŕ│╝ ŕ┤ÇŰáĘŰÉť Ýö╝ÝĽ┤ ýŁś ýáĽŰĆäŰą╝ ÝÖĽýŁŞÝĽť ÝŤä, ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłÝĽ┤ŕ▓░Ű░ęŰ▓ĽýŚÉ ŰîÇÝĽť ŰŐąŰáą ýŁä ÝľąýâüýőťÝéĄŰŐöŰŹ░ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŕ│á ÝĽá ýłś ý׳ŰőĄ (Stanton et al., 2005; Choi et al., 2008).
ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýéČÝĽşýŁä ýל ýŁ┤ÝľëÝĽťŰőĄŰę┤ ýÁťýćîÝĽť ŕ┤ÇŰŽČŰÉśýľ┤ýĽ╝ ÝĽá ýáĽŰ│┤Ű│┤ýĽłýéČÝĽşýŚÉ ŰîÇÝĽť ýÜöýćîŰą╝ ÝÖĽýŁŞÝĽá ýłś ý׳ŰőĄ. ýŁ┤Űą╝ ÝćÁÝĽ┤ ýἠŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä ýťäŰ░śÝĽśýžÇ ýĽŐŕ│á ýל ýŁ┤ÝľëÝĽťŰőĄŰę┤ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ۬ęÝĹťýÖÇ ŰÂÇÝĽęŰÉśŰŐö ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáą ýłśýĄÇýŁ┤ ÝľąýâüŰÉá ŕ▓âýŁ┤ŰőĄ(Park & Yim, 2012).ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůŰžî ýל ýŁ┤ÝľëÝĽśŰŐö ŕ▓âýŁÇ ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáą ÝľąýâüýŚÉ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŰŐö ŕ▓âýŁä ÝÖĽýŁŞÝĽśŕ│áý×É ÝĽťŰőĄ. Űö░ ŰŁ╝ýäť ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýäáÝľëýÜö ýŁŞýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁŕ│╝ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰíť ýäáýáĽÝĽśýŚČ ŕ░ÇýäĄ7 ŕ│╝ ŕ░ÇýäĄ8ýŁä ŰĆäýݼśýśÇŰőĄ.
[ŕ░ÇýäĄ7] ýí░ýžüŕÁČýä▒ýŤÉýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŚÉ ýáĽ(+) ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ8] ýí░ýžüýŁś Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰŐö ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŚÉ ýáĽ(+)ýŁś ýśüÝľą ýŁä Ű»Şý╣ťŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŁÇ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýőĄÝľëÝĽśŕŞ░ ýťäÝĽť ýí░ýžüŕÁČ ýä▒ýŤÉŰôĄýŁś ýőĄý▓ťýáüýŁŞ ÝľëŰĆÖýéČÝĽşýŁ┤ŰőĄ(Kim & Song, 2011).ýí░ýžüŕÁČ ýä▒ýŤÉŰôĄýŁ┤ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ýžÇŕ░üŰÉť ýŁŞýőŁýłśýĄÇýŁ┤ Űćĺýť╝Űę┤ ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽ┤ ýőĄý▓ťÝĽ┤ýĽ╝ ÝĽśŰŐö ýéČÝĽşŰôĄýŁä Ű░śýśüÝĽśýŚČ ýáĽŰ│┤Ű│┤ýĽł ýŁä ýťäÝĽť ŰůŞŰáąýŁä ýŁ┤ÝľëÝĽśŰŐö ÝľëŰĆÖýéČÝĽşýŁś ýáĽŰĆäŕ░Ç ŰćĺýĽäýžł ŕ▓âýŁ┤ŰőĄ (Lee et al. 2004; Chen et al., 2008).
ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ů ýéČÝĽşýŁä ýĄÇýłśÝĽśŰŐö ŕ▓âýŁÇ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ ýĽłŕ│╝ ŕ┤ÇŰáĘŰÉť ýáĽý▒ůŕŞ░Ű░ś ýŚůŰČ┤ýéČÝĽşýŁś ýáüýÜęýä▒ ÝľąýâüýŚÉŰĆä ŕŞ░ýŚČÝĽťŰőĄ (Geordie & David, 2012). ŰśÉÝĽť ýí░ýžüýŁś Ű│┤ýĽłÝÖťŰĆÖ ÝľëŰĆÖýŁś ýťáýÜę ýä▒ŕ│╝ ÝÜĘŕ│╝ýä▒ýŚÉ ŰîÇÝĽť ŰĆäýŤÇýŁä ýú╝ŕ│áý×ÉÝĽśŰŐö ýéČÝĽşýŁä ÝĆČÝĽĘÝĽśŕ│á ý׳ŕŞ░ ýŚÉ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ÝľëŰĆÖýŚÉ એýáĽýáüýŁŞ ýśüÝľąýŁä Ű»Şý╣á ŕ▓â ýŁ┤ŰőĄ. Űö░ŰŁ╝ýäť ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýäáÝľëýÜöýŁŞýť╝Űíť ýἠŰ│┤Ű│┤ýĽłýŁŞýőŁŕ│╝ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰíť ýäáýáĽÝĽśýŚČ ŰőĄýŁîŕ│╝ ŕ░ÖýŁÇ ŕ░Ç ýäĄ9, ŕ░ÇýäĄ10ýŁä ýłśŰŽŻÝĽśýśÇŰőĄ.
[ŕ░ÇýäĄ9] ýí░ýžüŕÁČýä▒ýŤÉýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŚÉ ýáĽ(+) ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ10] ýí░ýžüýŁś Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰŐö ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŚÉ ýáĽ(+)ýŁś ýśü ÝľąýŁä Ű»Şý╣ťŰőĄ.
ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ŰŐö ýí░ýžü Űé┤/ýÖŞŰÂÇýáüýŁŞ Ýö╝ÝĽ┤ýŁś ýćÉýőĄýŁä ŕ░ÉýćîýőťÝéĄŕ│á ÝÜĘŕ│╝ýáüýŁŞ ýí░ýžü Ű│┤ýĽłýŁä ÝĆëŕ░ÇÝĽá ýłś ý׳ŰŐö ýä▒ŕ│╝ýáüýŁŞ ýŞíŰę┤ýŁä ÝÖĽýŁŞÝĽśŰŐö ýéČÝĽşýť╝Űíť ÝÖĽýŁŞÝĽá ýłś ý׳ŰőĄ(Ha & Kim, 2013). ýí░ýžü Ű│┤ýĽłýéČŕ│á Ű░ťýâŁýŚÉ ŰîÇÝĽť Ýö╝ÝĽ┤ýŁś ýćÉýőĄýŁä ŕ░ÉýćîýőťÝéČ ýłś ý׳ŰŐö ýžÇ ýáĽŰ│┤ýťáýÂť Ýö╝ÝĽ┤ ŕ̝۬ĘýŚÉ ŰîÇÝĽť ŕ░Éýćî, ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ýĽłýáäýä▒ ŕ│╝ ýí░ýžüýŁś Ű│┤ýĽłŕ┤ÇŰŽČ ýÜöŕÁČýéČÝĽşýŚÉ ŰîÇÝĽť ýÂęýí▒ŰĆäŰíť ÝĆëŕ░ÇÝĽťŰőĄ (Park, 2007). ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś Ű│┤ýĽłŰŐąŰáąýłśýĄÇýŁ┤ ŰćĺŰőĄŰŐö ŕ▓âýŁÇ ýí░ ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝Űą╝ ŰćĺýŁ┤ŰŐöŰŹ░ ýśüÝľąýŁä Ű»Şý╣á ŕ▓âýŁ┤ŰőĄ.
ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýí░ýžü ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ÝľëŰĆÖýŁÇ ýí░ýžüŰ│┤ýĽł ýéČ ÝĽşýŁä ýéČýáäýŚÉ ýőĄý▓ťÝĽśŕ│á ýŁ┤ÝľëÝĽśŰŐö ŕ▓âýŁ┤ŰőĄ. ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ Űíť ÝÖĽýŁŞÝĽá ýłś ý׳ŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýéČŕ│á ýćÉýőĄýŚÉ ŰîÇÝĽť ŕ░ÉýćîýÖÇ ýáĽŰ│┤ýťáýÂťÝö╝ÝĽ┤ ŕ̝۬ĘýŁś ŕ░Éýćî, ýí░ýžüýáĽŰ│┤Ű│┤ýĽłýŁś ýĽłýáäýä▒ŕ│╝ ýí░ýžü Űé┤ ýáĽŰ│┤Ű│┤ýĽł ýÜöŕÁČýéČÝĽş ýÂęýí▒ŰĆäýŁś Ýľąýâüýť╝Űíť ÝÖĽýŁŞÝĽá ýłś ý׳ýť╝Űę░ (Kankanhalli et al., 2003; Geordie & David, 2012), ýŁ┤ŰŐö ýáĽŰ│┤ Ű│┤ýĽłýä▒ŕ│╝ýŚÉ એýáĽýáüýŁŞ ýä▒ŕ│╝Űą╝ ŕ░ÇýáŞŰőĄ ýĄä ŕ▓âýŁ┤ŰőĄ. Űö░ŰŁ╝ýäť ýí░ýžü ýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýÖÇýŁś ŕ┤Çŕ│äýŚÉýäť ýśüÝľąŰáą ý׳ŰŐö ýäáÝľëýÜöýŁŞýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáą, ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýť╝Űíť ýäáýáĽÝĽśýŚČ ŰőĄýŁîŕ│╝ ŕ░ÖýŁÇ ŕ░ÇýäĄ 11ŕ│╝ ŕ░ÇýäĄ12Űą╝ ýłśŰŽŻÝĽśýśÇŰőĄ.
[ŕ░ÇýäĄ11] ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŁÇ ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýἠ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
[ŕ░ÇýäĄ12] ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŁÇ ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýἠ(+)ýŁś ýśüÝľąýŁä Ű»Şý╣ťŰőĄ.
Ű│Ş ýŚ░ŕÁČ۬ĘÝśĽŕ│╝ ŕ░ÇýäĄýäĄýáĽýŚÉ ýéČýÜęÝĽť ŕÁČýä▒ŕ░ťŰůÉýŚÉ ŰîÇÝĽť ýí░ý×Ĺýáü ýáĽýŁśýÖÇ ýŞíýáĽÝĽşŰ¬ęýŁÇ ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. ýÜ░ýäá ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäŰŐö ÝśŞýŁśýáü ýŁŞ ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäŰą╝ ÝśĽýä▒ÝĽśŕŞ░ ýťäÝĽ┤ ýí░ýžüŕÁČýä▒ýŤÉýŁ┤ ýłśÝľëÝĽá ýłś ý׳ ŰŐö ýí░ýžüýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ÝľëŰĆÖýť╝Űíť ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞýť╝Űę░, ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö ýŐĄÝîŞŰęöýŁ╝ÝĽäÝä░Űžü, ý╗┤ÝôĘÝä░ýŁś ýĽłýáäýä▒ ÝÖĽýŁŞ, ÝîĘýŐĄ ýŤîŰôť Ű╣äŰůŞýÂť, Ű░▒ýőáýäĄý╣śŰíť ŕÁČýä▒ÝĽśýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰŐö ýí░ýžü ýŁś ýáĽŰ│┤Ű│┤ýĽł ÝÖťŰĆÖýŁä ýťäÝĽť Ű│┤ýĽł ŕ┤ÇŰáĘ ýéČÝĽşŰôĄýŁś ŕ┤ÇýőČýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞýť╝Űę░, ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ýĽł ýÁťýőáýáĽŰ│┤ ýŐÁŰôŁýŁś ŕ┤ÇýőČŰĆä, ýáĽŰ│┤Ű│┤ýĽł ÝöäŰíťŕĚŞŰ×Ę ýŚůŰŹ░ýŁ┤ÝŐŞýŚÉ ŕ┤ÇÝĽť ŕ┤ÇýőČŰĆä, ÝĽ┤ý╗Ą ý╣ĘÝłČ ŕ░ÇŰŐąýä▒ýŁś ŕ┤ÇýőČŰĆä, ŕ░ťýŁŞýáĽŰ│┤ ŰĆäýÜę Ýö╝ÝĽ┤ýÜ░ŰáĄýŁś ŕ┤ÇýőČ ŰĆäŰíť ýäáýáĽÝĽśýśÇŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁÇ ýí░ýžü Űé┤ ŕĚťýáĽŰÉť ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁ┤ ýáĽŰ│┤Ű│┤ýĽł ýŁä ýťäÝĽ┤ ýל ŕĚťýáĽŰÉśýŚłŰőĄŕ│á ýâŁŕ░üÝĽśŰŐö એýáĽýáüýŁŞ ýŞíŰę┤ýŁś ýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞŰőĄ. ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ýĽłýŁś ýĽłýáäýä▒, ýőá Űó░ýä▒, ýÜ░ýłśýä▒, ýŚůŰČ┤Ű│┤ýĽł ýáüýÜęýä▒ýť╝Űíť ýäáýáĽÝĽśýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłý▓śŰ▓î ýŁÇ ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁä ýĄÇýłśÝĽśýžÇ ýĽŐýĽśýŁä ŰĽî ŰĆîýĽäýśĄŰŐö ŰÂłýŁ┤ýŁÁýŁ┤ ŕ░Ç ÝĽ┤ ýžł ýłś ý׳ŰŐö ýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞýť╝Űę░, ýâüýťäŕ┤ÇŰŽČý×É ýŁś ÝćÁŰ│┤ý▓śŰ▓î, ýőťýŐĄÝůť ýéČýÜę ýáťÝĽťýŁś ý▓śŰ▓î, ŰÂłýŁ┤ýŁÁýŚÉ ŰîÇÝĽť ý▓śŰ▓î, ýŚůŰČ┤ÝÖťŰĆÖýŁś ýáťÝĽťýŁś ý▓śŰ▓îŰíť ŕÁČýä▒ÝĽśýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁÇ ýí░ýžü ýŁś ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŚÉ ŰîÇÝĽť ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýŁŞýžÇŰÉť ÝÜĘýÜęýä▒ ýáĽŰĆä ŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞýť╝Űę░, ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁś ýťáýŁÁýä▒, ýáüÝĽę ýä▒, ýáĽŰ│┤Ű│┤ÝśŞ ÝÖťŰĆÖýä▒, ýí░ýžü ýŚůŰČ┤ýáüýÜęýä▒ýť╝Űíť ýŞíýáĽÝĽşŰ¬ęýŁä ýäáýáĽÝĽś ýśÇŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁÇ ýí░ýžüýŚÉýäť Ű░ťýâŁÝĽá ýłś ý׳ŰŐö ýáĽŰ│┤Ű│┤ýĽł ýťäÝŚśýä▒ ýŚÉ ŰîÇÝĽť Ű│┤ýĽłŕŞ░ýłáýŁ┤Űéś Ű│┤ýĽłŕ┤ÇŰŽČ ŰîÇý▓śýŚÉ ŰîÇÝĽť ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ýŁŞýőŁýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞŰőĄ. ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁä ýŞíýáĽÝĽś ŕŞ░ ýťäÝĽť ÝĽşŰ¬ęýť╝ŰíťŰŐö. ýí░ýžü ýáĽŰ│┤ý×Éýé░ýŁś ýĄĹýÜöýä▒, ýí░ýžü ýáĽŰ│┤Ű│┤ýĽł ýťäÝśĹýŁŞýőŁ, ýí░ýžü Ű│┤Ű│┤ýĽłýĚĘýĽŻýä▒ ýŁŞýőŁ, ýí░ýžü ýáĽŰ│┤Ű│┤ýĽł ýőťýŐĄÝůť ŕ┤Ç ŰŽČ ýĄĹýÜöýä▒ ýŁŞýőŁ Űô▒ýť╝Űíť ýäáýáĽÝĽśýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśŰŐö ýí░ýžü ýŁś ýáĽŰ│┤Ű│┤ýĽłŕ│╝ ŕ┤ÇŰáĘŰÉť ýáĽý▒ů, ŕ░ÇýŁ┤ŰôťŰŁ╝ýŁŞýŁä ýĄÇýłśÝĽá ŰĽî ýáĽŰ│┤Ű│┤ ýĽł ÝÖťŰĆÖýŚÉ ŰĆäýŤÇýŁä ýú╝ŰŐö ýéČÝĽşýŁś ýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤Ű᪠ŰőĄ. ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö Ű│┤ýĽłýáĽý▒ůŕŞ░Ű░ś ýŚůŰČ┤Ű│┤ýĽłýŁś ýáüýÜęýä▒, Ű│┤ýĽłýἠý▒ůŕŞ░Ű░ś Ű│┤ýĽłÝÖťŰĆÖ ÝľëŰĆÖýŁś ýťáýÜęýä▒, Ű│┤ýĽłýáĽý▒ůŕŞ░Ű░ś Ű│┤ýĽłÝÖťŰĆÖ ÝÖĽýŁŞ ýŁś ýťáýÜęýä▒, Ű│┤ýĽłýáĽý▒ůŕŞ░Ű░ś Ű│┤ýĽłÝÖęŰĆÖÝÖĽýŁŞýŁś ÝÜĘŕ│╝ýä▒ýť╝Űíť ŕÁČýä▒ÝĽś ýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŁÇ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ýéČÝĽşýŚÉ ŰîÇÝĽ┤ ýŁ┤ÝĽ┤ÝĽśŰę░, ÝĽ┤ŕ▓░ÝĽá ýłś ý׳ŕ│á ýáĽŰ│┤Ű│┤ýĽłŕŞ░ýłáýŁä ýáüýÜęÝĽá ýłś ý׳ŰŐö ŰŐąŰáąýŁś ýáĽŰĆä ŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞŰőĄ. ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö ýáĽŰ│┤Ű│┤ýĽł Ýö╝ÝĽ┤ýŁŞ ýőŁ, ýáĽŰ│┤Ű│┤ýĽł ŕŞ░ýłáýéČýÜęŰ░ęŰ▓Ľ, ýáĽŰ│┤Ű│┤ýĽłŕŞ░ýłá ÝÖťýÜęŰĆä, ýáĽŰ│┤Ű│┤ýĽł ŰČŞýáťÝĽ┤ŕ▓░Űíť ŕÁČýä▒ÝĽśýśÇŰőĄ. ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖýŁÇ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁä ýőĄÝľëÝĽśŕŞ░ ýťäÝĽť ýí░ýžüŕÁČýä▒ýŤöŰô▒ýŁś ýőĄý▓ťýáüýŁŞ ÝľëŰĆÖýéČÝĽş ýáĽŰĆäŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞýť╝Űę░, ýŞíýáĽÝĽşŰ¬ęýť╝ŰíťŰŐö ýáĽŕŞ░ýáüýŁŞ ÝîĘýŐĄýŤîŰôť Ű│Çŕ▓Ż, ýáĽŰ│┤Ű│┤ÝśŞýőĄýáĽ, ýŚůŰČ┤ŰČŞýäťý░ĘŕŞ░, ýÂťý▓śŕ░Ç Ű¬ůÝÖĽÝĽť ÝîîýŁ╝ ŰőĄýÜ┤ ŰíťŰôťŰíť ýäáýáĽÝĽśýśÇŰőĄ.
ŰžłýžÇŰžëýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽł ÝÖťŰĆÖýť╝Űíť ýŁŞ ÝĽť ýí░ýžü Űé┤ŰÂÇýáü, ýÖŞŰÂÇýáüýŁŞ Ýö╝ÝĽ┤ýŁś ýćÉýőĄýŁä ŕ░ÉýćîýőťÝéĄŕ│á ýí░ýžüŰ│┤ ýĽłýŁä ÝĆëŕ░ÇÝĽá ýłś ý׳ŰŐö ýä▒ŕ│╝ ýéČÝĽşýŁ┤ŰŁ╝ŕ│á ýí░ý×Ĺýáü ýáĽýŁśŰą╝ Űé┤ŰáŞŰőĄ. ýŁ┤Űą╝ ýŞíýáĽÝĽśŕŞ░ ýťäÝĽť ÝĽşŰ¬ęýť╝ŰíťŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýéČŕ│á ýćÉýőĄ ŕ░É ýćî, ýí░ýžüýŁś ýáĽŰ│┤ýťáýÂť Ýö╝ÝĽ┤ ŕĚťŰ¬Ę ŕ░Éýćî, ýí░ýžüýáĽŰ│┤Ű│┤ýĽłýŁś ýĽłýáäýä▒ ÝÖĽŰ│┤, ýí░ýžüýáĽŰ│┤Ű│┤ýĽł ŕ┤ÇŰáĘ ýÜöŕÁČýéČÝĽş ýÂęýí▒ŰĆä Ýľąýâüýť╝Űíť ŕÁČýä▒ÝĽś ýśÇŰőĄ. ۬ĘŰôá ýŞíýáĽÝĽşŰ¬ęýŁÇ ŰŽČý╗ĄÝŐŞ(Likert) 7ýáÉ ý▓ÖŰĆäŰíť ýäĄŰČŞÝĽşŰ¬ęýŁä ŕÁČýä▒ÝĽśýśÇŰőĄ.
ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ýőĄýŽŁýáüýť╝Űíť ŰÂäýäŁÝĽśŕŞ░ ýťäÝĽť ÝĹťŰ│Ş ýžĹŰőĘýť╝Űíť ÝĽ┤ýÜ┤ÝĽşŰžîýí░ýžüýŚÉ ýóůýéČÝĽśŕ│á ý׳ŰŐö ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁä ŰîÇýâüýť╝Űíť ýäĄŰČŞýŁä ýłśÝľëÝĽśýśÇŰőĄ. Ű│Ş ýŚ░ŕÁČŰŐö ŕÁČýí░ Ű░ęýáĽýőŁ ۬ĘÝśĽýŁä ýŁ┤ýÜęÝĽśýŚČ ýŁŞŕ│╝ýÜöýŁŞýŁä ŰĆäýݼśýśÇýť╝Űę░ ýłśýžĹŰÉť ŰŹ░ ýŁ┤Ýä░Űą╝ ýőĄýŽŁ ŰÂäýäŁÝĽśýśÇŰőĄ. ý┤Ł 150ŕ░ťýŁś ýäĄŰČŞýžÇŰą╝ Ű░░ŰÂÇÝĽśýŚČ 150 ŕ░ťýŁś ýäĄŰČŞýŁä ÝÜîýłśÝĽśýśÇýť╝Űę░, ŕ▓░ýŞíý╣śŕ░Ç ý׳ŕ▒░Űéś ŰÂłýä▒ýőĄÝĽśŕ▓î ýŁĹŰőÁ ÝĽť ýäĄŰČŞýžÇ 5ŰÂÇŰą╝ ýáťýÖŞÝĽť ý┤Ł 145ŰÂÇŕ░Ç Ű│Ş ýŚ░ŕÁČýŁś ýÁťýóůŰÂäýäŁýŚÉ ýéČ ýÜęŰÉśýŚłŰőĄ.
Table 1ýŁÇ ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžü ýŁĹŰőÁý×ÉýŁś ýí░ýžüŰ│┤ýĽł ŕ┤ÇŰáĘ ÝŐ╣ýä▒ýŁ┤ ŰőĄ. ýí░ýžü Űé┤ Ű│┤ýĽłýáäŰő┤ýí░ýžüýŁ┤ ýťá/ŰČ┤ýŚÉýäť ý׳ŰőĄŕ░Ç 113۬ů(77.9%), ýŚćŰőĄŕ░Ç 32۬ů(22.1%)Űíť ŰéśÝâÇŰéČŰőĄ. Ű│┤ýĽłýáĽý▒ů ýťá/ŰČ┤ýŚÉýäťŰŐö ý׳ŰőĄ ŕ░Ç 135۬ů(93.1%), ýŚćŰőĄŕ░Ç 10۬ů(6.9%)Űíť ŰÂäýäŁŰÉśýŚłŰőĄ. ŰśÉÝĽť Ű│┤ýĽł ý▓śŰ▓îýŁÇ ý׳ŰőĄŕ░Ç 110۬ů(75.9%), ýŚćŰőĄŕ░Ç 35۬ů(24.1%)Űíť ŰÂäýäŁŰÉśýŚł ŰőĄ. ýŚ░ŕ░ä Ű│┤ýĽłŕÁÉýťíýŁä Ű░ŤŰŐö ÝÜčýłśŰŐö 1ÝÜîŕ░Ç 59۬ů(40.7)Űíť ŕ░Çý׹ Űćĺ ýŁÇ Ű╣äýťĘýŁä ý░ĘýžÇÝĽśŕ│á ý׳ýŚłýť╝Űę░ 2~3ÝÜîŕ░Ç 54۬ů(37.2%)ýť╝Űíť ŰéśÝâÇ ŰéČŰőĄ.
Characteristics of the sample
ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžüýŁś ÝĹťŰ│Ş ýžĹŰőĘýŁä ŰîÇýâüýť╝Űíť ŰÂäýäŁÝĽť ŕÁČýä▒ŕ░ťŰůÉ Ű│ä ŰőĘýŁ╝ý░ĘýŤÉýä▒ýŁä ýáÇÝĽ┤ÝĽśŰŐö ýŞíýáĽŰ│ÇýłśŰŐö ÝĹťýĄÇÝÖö ý×öý░ĘýÖÇ ýłśýáĽýžÇ ýłśŰíť ŰéśÝâÇŰéťŰőĄ. ÝĹťýĄÇÝÖö ý×öý░Ęŕ░Ç ýťáýŁśÝĽť ýłśýĄÇýŁä ýžÇŰéśý╣śŕ▓î Ű▓Śýľ┤ Űéśŕ▒░Űéś ýłśýáĽýžÇýłśýŁś ŕ░ĺýŁ┤ 5Űą╝ Űäśýľ┤ýäťŰŐö ýŞíýáĽŰ│ÇýłśŰôĄ ŕ░äýŁś ŕ┤Çŕ│ä ýŚÉ ŰîÇÝĽ┤ýäť ŕ░ü ýŞíýáĽÝĽşŰ¬ęŰôĄýŁä ۬ĘÝśĽýŁś ÝâÇŰő╣ýä▒ ŕ▓ÇýáĽýŁä ýťäÝĽ┤ýäť ŰőĘ ŕ│äýáüýť╝Űíť ýáťŕ▒░ÝĽ┤ Űéśŕ░ÇŰŐö Ű░ęŰ▓ĽýŁä ýéČýÜęÝĽśýŚČ ÝÖĽýŁŞýáü ýÜöýŁŞŰÂäýäŁýŁä ýőĄýőťÝĽśýśÇŰőĄ. ÝÖĽýŁŞýáü ýÜöýŁŞŰÂäýäŁýŁä ÝćÁÝĽ┤ ýÂöýÂťŰÉť 40ŕ░ťýŁś ýŞíýáĽÝĽşŰ¬ę ýĄĹýŚÉýäť ýáĽŰ│┤Ű│┤ýĽłÝâťŰĆäýŚÉýäť SA2 ÝĽşŰ¬ę, ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäýŚÉýäť SI1, ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŚÉýäť SS3, ýáĽŰ│┤Ű│┤ýĽłý▓śŰ▓îýŚÉýäť SP3, ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťí ýŚÉýäť SE2, ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁ AW3, ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉýäť POL3, ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáą AB1, ýáĽŰ│┤Ű│┤ýĽłÝľëŰĆÖ SB2, ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ ÝĽşŰ¬ęýŚÉ ýäť ISP4 ÝĽşŰ¬ęýŁś 10ŕ░ťýŁś ÝĽşŰ¬ęýŁ┤ ÝĹťýĄÇÝÖöŰÉť ý×öý░ĘýÖÇ ýłśýáĽýžÇýłśŕ░Ç ÝüČŕ▓î ŰéśÝâÇŰéś ýŁ┤ŰôĄ ÝĽşŰ¬ęýŁä ýáťýÖŞÝĽť 30ŕ░ťýŁś ÝĽşŰ¬ęýŚÉ ŰîÇÝĽśýŚČ ýÁťýóů ýáüýť╝Űíť ŕÁČýí░Ű░ęýáĽýőŁýŁä ýŁ┤ýÜęÝĽť ýŞíýἠݼśŰÂÇ۬ĘÝśĽýŁä ýőĄýŽŁ ŰÂäýäŁÝĽśýśÇ ŰőĄ.
Ű│Ş ýŚ░ŕÁČýŁś ýŞíýἠݼśŰÂÇ۬ĘÝśĽýŁś ýőáŰó░ýä▒ýŁä ÝĆëŕ░ÇÝĽśŕŞ░ ýťäÝĽ┤ ÝĽęýä▒ ŕ░ťŰůÉýőáŰó░ŰĆä, ÝĆëŕĚáŰÂäýé░ýÂöýÂť ŕ░ĺ, Cronbach-╬▒ŕ░ĺýŁä Table 2ýŚÉ ýáť ýőťÝĽśýśÇŰőĄ. ŕÁČýä▒ŕ░ťŰůÉýŚÉ ýŁśÝĽ┤ ýäĄŰ¬ůŰÉśŰŐö ŰÂäýé░ýŁś ýľĹýŁä ŰéśÝâÇŰé┤ŰŐö ÝĆëŕĚáŰÂäýé░ýÂöýÂť ŕ░ĺ(AVE)ýŁ┤ 0.5Űą╝ ýâüÝÜîÝĽśŰę░, ŕ░ü ýŞíýáĽÝĽşŰ¬ęýŁś ýÂöýἠý╣śŕ░Ç 0.5ýŁ┤ýâü, ŕĚŞ ýÂöýáĽý╣śýŁś t-ŕ░ĺýŁ┤ 2.0ýŁ┤ýâüýť╝Űíť ŰéśÝâÇŰéś ýžĹýĄĹÝâÇ Űő╣ýä▒ýŁ┤ ŰćĺýŁÇ ŕ▓âýŁä ÝÖĽýŁŞÝĽśýśÇýť╝Űę░, Cronbach-╬▒ŕ░ĺýŁ┤ 0.7ýŁ┤ýâüýť╝ Űíť ŰéśÝâÇŰéś ýłśýÜęŕŞ░ýĄÇýŚÉ ŰÂÇÝĽęÝĽśŰŐö ŕ▓░ŕ│╝Űą╝ ÝÖĽýŁŞÝĽśýśÇŰőĄ.
Measurement model analysis
ýĽäŰלýŁś Table 3ýŚÉ ýáťýőťŰÉť ýŞíýáĽŰ¬ĘÝśĽýŁś ÝîÉŰ│äÝâÇŰő╣ýä▒ ŕ▓░ŕ│╝Űą╝ Ű│┤Űę┤ ŕ░ü ŕÁČýä▒ŕ░ťŰůÉŰôĄýŁś ÝĆëŕĚáŰÂäýé░ýÂöýÂť ŕ░ĺýŁś ýáťŕ│▒ŕĚ╝ýŁ┤ ŰőĄŰąŞ ŕÁČýä▒ ŕ░ťŰůÉŰôĄ ŕ░äýŁś ýâüŕ┤Çŕ│äýłśŰ│┤ŰőĄ ýâüÝÜîÝĽśŰŐö ŕ▓âýť╝Űíť ŰéśÝâÇŰéś ÝîÉŰ│äÝâÇŰő╣ ýä▒ýŁä ÝÖĽýŁŞÝĽśýśÇŰőĄ. ÝĽť ŕÁČýä▒ŕ░ťŰůÉ Űé┤ýŚÉýäťýŁś ýŞíýáĽÝĽşŰ¬ęŰôĄýŁÇ ý×Éý▓┤ ŰíťŰöęÝĽť ŕ░ĺýŁ┤ ŰőĄŰąŞ ŕÁČýä▒ŕ░ťŰůÉŕ│╝ýŁś ÝüČŰíťýŐĄ ŰíťŰöęÝĽť ŕ░ĺŰ│┤ŰőĄ Ýü░ŕ░ÇŰą╝ ýŞíýáĽÝĽśýŚČ ÝîÉŰ│äÝâÇŰő╣ýä▒ýŁä ŕ▓ÇýŽŁ ÝĽśýśÇŰőĄ.
Determination Validity (AVE)
Table 4ŰŐö ýŞíýáĽŰ¬ĘÝśĽýŁś ýáüÝĽęŰĆäýÖÇ ŕÁČýí░۬ĘÝśĽýŚÉ ŰîÇÝĽť ýáüÝĽęŰĆä ýžÇýłśŰą╝ ŰéśÝâÇŰéŞ ŕ▓░ŕ│╝ýŁ┤ŰőĄ. ýÜ░ýäá ýŞíýáĽŰ¬ĘÝśĽýŚÉ ý׳ýľ┤ýäť ¤ç2 (p)ŰŐö 551.28(0.00)ýŁ┤ŕ│á, ¤ç2ýŁä ý×ÉýťáŰĆäŰíť ŰéśŰłł Ű╣äýťĘýŁ┤ 1.55Űíť ŰéśÝâÇŰéś ŕÂîý׹ýłśýĄÇ(ÔëĄ3.00)ýŁä Űžîýí▒ýőťÝéĄŰŐö ŕ▓âýť╝Űíť ŰÂäýäŁŰÉśýŚłŰőĄ. GFIŕ░Ç 0.814, AGFIŕ░Ç 0.76ýť╝Űíť ŕÂîý׹ýłśýĄÇŰ│┤ŰőĄ ýí░ળ Űé«ŕ▓î ŰéśÝâÇŰéČýžÇŰžî ýŚ░ŕÁČ۬ĘÝśĽýŁ┤ ýľ╝ŰžłŰéś ýל ŕĚ╝ýéČÝĽśŰŐÉŰâÉýŁś ýáĽŰĆäŰą╝ ŰéśÝâÇŰé┤ŰŐö RMSEA ŕ░ĺýŁ┤ 0.06ýť╝Űíť ŕÂîý׹ýłśýĄÇýŁä Űžîýí▒ÝĽśýśÇŰőĄ. ŕĚŞŰŽČŕ│á 1.0ýŚÉ ŕĚ╝ýéČÝĽá ŕ▓ŻýÜ░ ýáüÝĽęÝĽśŰőĄŕ│á Ű│╝ ýłś ý׳ŰŐö IFIŕ░Ç 0.93, CFIŕ░Ç 0.93, ŕ░ä۬ůŰÂÇÝĽęýžÇýłś PGFI, PNFIŕ░Ç ŕ░üŕ░ü 0.62, 0.68Űíť ŰéśÝâÇŰéČýť╝Űę░ ýáü ÝĽęŰĆä ýžÇýłś ۬ĘŰĹÉ ŰîÇý▓┤ýáüýť╝Űíť ýŞíýáĽŰ¬ĘÝśĽýŁś ýáüÝĽęŰĆäŕ░Ç ýłśýÜęŕŞ░ýĄÇýŁä ýÂęýí▒ÝĽśŰŐö ŕ▓âýť╝Űíť ÝĆëŕ░ÇÝĽśýśÇŰőĄ.
Goodness of fit index
ŰőĄýŁîýť╝Űíť ŕÁČýä▒ŕ░ťŰůÉýŁś ŕÁČýí░ýáü ŕ┤Çŕ│äŰą╝ ýäĄŰ¬ůÝĽśŰŐö ŕÁČýí░۬ĘÝśĽýŚÉ ŰîÇÝĽť ýáüÝĽęŰĆä ýžÇýłśŰą╝ Ű│┤Űę┤¤ç2 (p)ŰŐö 584.62(0.00)ýŁ┤ŕ│á, ¤ç2ýŁä ý×É ýťáŰĆäŰíť ŰéśŰłł Ű╣äýťĘýŁ┤ 1.57Űíť ŰéśÝâÇŰéś ŕÂîý×áýłśýĄÇ(ÔëĄ3.00)ýŁä Űžîýí▒ýőť ÝéĄŰŐö ŕ▓âýť╝Űíť ŰÂäýäŁŰÉśýŚłŰőĄ. ýŞíýáĽŰ¬ĘÝśĽ ŕ▓░ŕ│╝ýÖÇ ýťáýéČÝĽśŕ▓î GFIŕ░Ç 0.808, AGFIŕ░Ç 0.76ýť╝Űíť ŕÂîý׹ýłśýĄÇŰ│┤ŰőĄ ýí░ળ Űé«ŕ▓î ŰéśÝâÇŰéČýžÇŰžî ýŚ░ŕÁČ۬ĘÝśĽýŁ┤ ýľ╝ŰžłŰéś ýל ŕĚ╝ýéČÝĽśŰŐÉŰâÉýŁś ýáĽŰĆäŰą╝ ŰéśÝâÇŰé┤ŰŐö RMSEA ŕ░ĺýŁ┤ 0.06ýť╝Űíť ŕÂîý׹ýłśýĄÇýŁä Űžîýí▒ÝĽśŕ│á, 1.0ýŚÉ ŕĚ╝ýéČÝĽá ŕ▓Ż ýÜ░ ýáüÝĽęÝĽśŰőĄŕ│á Ű│╝ ýłś ý׳ŰŐö IFIŕ░Ç 0.93, CFIŕ░Ç 0.93, ŕ░ä۬ůŰÂÇÝĽęýžÇ ýłś PGFI, PNFIŕ░Ç ŕ░üŕ░ü 0.65, 0.7Űíť ŰéśÝâÇŰéś ŕÂîý׹ýłśýĄÇýŚÉ ŰÂÇÝĽęÝĽś ŰŐö ŕ▓âýť╝Űíť ŰÂäýäŁŰÉśýŚłŰőĄ.
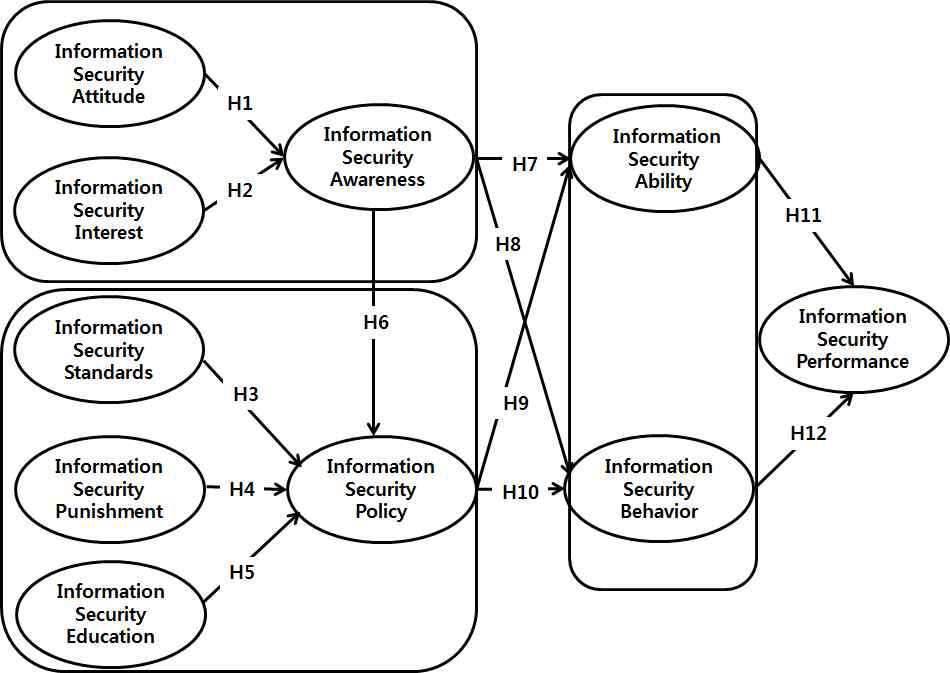
ŕÁČýí░۬ĘÝśĽýŁś ŰÂäýäŁŕ▓░ŕ│╝ýŚÉ Űö░ŰąŞ ýŚ░ŕÁČŕ░ÇýäĄ ŕ▓ÇýáĽŕ▓░ŕ│╝Űą╝ ŕ░ü ŕ▓ŻŰíť ýŁś ýÂöýáĽý╣śýÖÇ t-ŕ░ĺýť╝Űíť ŰéśÝâÇŰé┤Űę┤ ŰőĄýŁîýŁś Fig. 2ýŚÉýäť Ű│┤ŰŐö Ű░öýÖÇ ŕ░ÖŰőĄ. ýáĽŰ│┤Ű│┤ýĽłý▓śŰ▓îŕ│╝ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłś ŕ░äýŁś ŕ┤Çŕ│äŰą╝ ŕ▓ÇýáĽÝĽś ŰŐö ýŚ░ŕÁČŕ░ÇýäĄ4(H4) ŕ▓ŻŰíťýÖÇ ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁ┤ ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłś ýŚÉ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŰŐö ýŚ░ŕÁČŕ░ÇýäĄ5(H5)Űą╝ ýáťýÖŞÝĽť ŰőĄŰąŞ ۬ĘŰôá ŕ▓ŻŰíť ŰŐö ÝćÁŕ│äýáüýť╝Űíť ýťáýŁśÝĽť ŕ▓âýť╝Űíť ÝÖĽýŁŞŰÉśýľ┤ ýŚ░ŕÁČ ŕ░ÇýäĄŰôĄýŁ┤ ý▒äÝâŁŰÉś ýŚłŰőĄ. ýÁťýóůýáüýŁŞ ŕ░ÇýäĄ ŕ▓ÇýŽŁ ŕ▓░ŕ│╝ŰŐö Table 5ýÖÇ ŕ░ÖŰőĄ.
Results of hypothesis testing
Ű│Ş ýŚ░ŕÁČŰą╝ ÝćÁÝĽ┤ ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžü ŕÁČýä▒ýŤÉŰôĄýŁ┤ ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇ ÝĽť એýáĽýáüýŁŞ Ű│┤ýĽłÝâťŰĆäŰą╝ ŕ░ÇýžÇŕ│á ýáĽŰ│┤Ű│┤ýĽłŕ┤ÇýőČŰĆäŰą╝ Űćĺŕ▓î Ű│┤ýŁ╝ ŰĽî ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁ ýłśýĄÇýŚÉ ýśüÝľąýŁä Ű»Şý╣ťŰőĄŰŐö ŕ▓âýŁä ÝÖĽýŁŞÝĽá ýłś ý׳ŰőĄ. ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłŕĚťŰ▓öýŁÇ ÝĽ┤ýÜ┤┬ĚÝĽşŰžî ýí░ýžüýŁś ÝŐ╣ýä▒ýâü ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ŕ┤ÇŰŽČýáüýŁŞ ýŞíŰę┤ýŚÉýäť ýáĹŕĚ╝ÝĽá ýłś ý׳ŰŐö ÝŚłýÜęŰ▓öýťä Űą╝ ýí░ýžüýŁś ýťáÝśĽŰ│äŰíť ýí░ýžüýŁś ÝŐ╣ýä▒Ű│äŰíť ŕ░üŕ░üýŁś Ű│┤ýĽłŕĚťŰ▓öýŁ┤ ۬ůýőť ŰÉśýľ┤ ý׳ŰőĄ. ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýŁś ýőťýäĄŰ│┤ýĽłýŚÉ ŰîÇÝĽť ŕĚťŰ▓öýŁ┤ ýĽäŰőî ýáĽŰ│┤ Ű│┤ýĽłýŚÉ ŕ┤ÇÝĽť ŕĚťŰ▓öýŁ┤ŕŞ░ýŚÉ ýáĽŰ│┤ý×Éýé░ýŚÉ ŰîÇÝĽť ýĄĹýÜöýä▒ýŁä ýŁŞýőŁÝľłýŁä ŰĽî ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä Ű░śŰôťýőť ýĄÇýłśÝĽśŕ▓î ŰÉśŰŐö ŕ▓âýŁ┤ŰőĄ.
ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłý▓śŰ▓îŕ│╝ ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíýŁÇ ýőĄýáťŰíť ÝśĽýőŁýáüýť╝Űíť ŕĚťýáĽŰÉśýľ┤ ý׳ŕ│á ýőťÝľëÝĽśŰŐö ŕ▓ŻýÜ░ŕ░Ç ŰîÇŰÂÇŰÂäýŁ┤Űę░ ŕÁÉýťí Ű╣äýťĘýŁ┤ ŰćĺýžÇ ýĽŐŰőĄŰŐö ŕ▓âýŁä ýĽî ýłś ý׳ŰőĄ. ýí░ýžüýŚÉýäťýŁś ŕĚ╝Űíťŕ│äýĽŻýŁä Űž║ýŁä ŰĽîŰéś ŰžĄŰůä ýŚ░Ű┤ëŕ│äýĽŻýŁä ý▓┤ŕ▓░ÝĽá ŰĽî Ű│┤ýĽłŕ│╝ ŕ┤ÇŰáĘÝĽ┤ ýžÇý╝ťýĽ╝ ÝĽśŰŐö ýéČýĽłýŁä ýäĄŰ¬ůÝĽ┤ýú╝ŰŐö ŕ▓âŰĆä ýĄĹýÜöÝĽśŰőĄŕ│á ÝĽá ýłś ý׳ŰőĄ. ŰőĘýłťÝ׳ ýáĽŰ│┤Ű│┤ýĽłŕÁÉýťíŕ│╝ ý▓śŰ▓îýŚÉ ŰîÇÝĽť ýéČÝĽşýŁä ýžüýŤÉŰôĄýŁä ۬ĘýĽäŰćôŕ│á ÝĽśŰŐö ŕ▓âŰ│┤ŰőĄ, ýőĄŰČ┤ýáüýŁŞ ý░ĘýŤÉýŚÉýäť ŰžĘÝłČŰžĘýť╝Űíť ŕÁÉýťíÝĽśŰŐö Ű░ęŰ▓ĽŰĆä ÝĽäýÜö ÝĽśŰőĄŕ│á Ű│ŞŰőĄ. ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ýŁŞýőŁýŁś ýáĽŰĆäŕ░Ç ŰćĺýŁä ŰĽî ýáĽŰ│┤Ű│┤ ýĽłýáĽý▒ůýŁä ýĄÇýłśÝĽśŰŐöŰŹ░ ýśüÝľąŰáąýŁ┤ ý׳ŰőĄŰŐö ŕ▓âýŁä ÝÖĽýŁŞÝĽśýśÇŰőĄ. ýáĽŰ│┤ Ű│┤ýĽłýŁä ýŁŞýőŁÝĽťŰőĄŰŐö ŕ▓â ý×Éý▓┤ŕ░Ç ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąŕ│╝ ÝľëŰĆÖýŁä ýťäÝĽť ŰőĘ ŕ│äýáüýŁŞ ýáĽŰ│┤Ű│┤ýĽłÝÖťŰĆÖýŚÉ ýśüÝľąýŁä ýú╝ŰŐö ŰÂÇŰÂäýŁ┤ŰŁ╝ŕ│á Ű│╝ ýłś ý׳ŰőĄ.
ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýŁä ýĄÇýłśÝĽťŰőĄŰŐö ŕ▓âýŁÇ ýí░ýžüýŚÉýäť ŕ░Ľýí░ŰÉśŕ│á Ű░śŰôť ýőť ýžÇý╝ťýĽ╝ÝĽśŰŐö ýĄÇýłśýéČÝĽşýŚÉ ŰîÇÝĽ┤ ýŁ┤ÝĽ┤ÝĽśŕ│á ŕ▓ÇÝćáÝĽť ŰÂÇŰÂäýŁ┤ ýÂęŰÂä Ý׳ ŰćĺŰőĄŕ│á ÝîÉŰőĘÝĽá ýłś ý׳ýť╝Űę░ ýŁ┤ŰŐö ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ÝÜĘŕ│╝ýáüýŁŞ ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ŕ┤ÇŰŽČýáüýŁŞ ýŞíŰę┤ýŁś ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąŕ│╝ ÝľëŰĆÖýť╝Űíť ÝĹťýÂťŰÉťŰőĄŰŐö ŕ▓âýŁä ýĽî ýłś ý׳ŰőĄ. ýáĽŰ│┤Ű│┤ýĽłŰŐąŰáąýŁś ýłśýĄÇýŁ┤ Űćĺŕ│á ýἠŰ│┤Ű│┤ýĽłÝľëŰĆÖýŁ┤ ýŁ┤ŰĄäýžäŰőĄŰŐö ŕ▓âýŁÇ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýŚÉ ŰîÇÝĽť ýćÉýőĄ ýŁä ŕ░ÉýćîýőťÝéČ ýłś ý׳ŰŐö Ű░ęýĽłýť╝Űíť Ű¬ĘýâëÝĽśŕ│á ýáĽŰ│┤Ű│┤ýĽłýŁä ýťäÝĽť ýí░ ýžüýŁś ýä▒ŕ│╝ýžÇÝľąýŁä ýťäÝĽ┤ ŕ│ÁŰĆÖýŁś ۬ęÝŝ۹╝ ŰőČýä▒ÝĽá ýłś ý׳ŰőĄŕ│á Ű│╝ ýłś ý׳ŰőĄ.
Ű│Ş ýŚ░ŕÁČýŁś ýŁśýŁśŰíťŰŐö ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. ÝĽ┤ýÜ┤┬ĚÝĽşŰžîýí░ýžü Ű│┤ýĽłýŁś ÝŐ╣ýä▒ýť╝Űíť ýŚ░ŕ░ä Ű│┤ýĽłŕÁÉýťíýŁä ýőťÝľëÝĽśŰŐö ÝÜčýłśŕ░Ç 1ÝÜîŕ░Ç 40.7%, 2~ 3ÝÜîŕ░Ç 37.2%Űíť ŰéśÝâÇŰéś ÝĽ┤ýÜ┤ÝĽşŰžî ýáĽŰ│┤Ű│┤ýĽł ýťáýÂťýőť ÝîîŕŞëÝÜĘŕ│╝ýŚÉ ŰîÇÝĽť Ýö╝ÝĽ┤ŰŐö ýőČŕ░üýä▒ýŚÉ ŰîÇÝĽť ýí░ýžüýŁś Ű│┤ýĽłŕÁÉýťíýŚÉ ŰîÇÝĽť ŕ┤ÇŰŽČŕ░Ç ýőťŕŞëÝĽĘýŁä ýĽî ýłś ý׳ýŚłýť╝Űę░, Ű│┤ýĽłŕÁÉýťíýŁś ŕ░ĽÝÖöýÖÇ ÝĽĘŕ╗ś ýí░ýžüŕÁČýä▒ ýŤÉýŚÉŕ▓î ýí░ýžüŰ│┤ýĽłýŁś ýĄĹýÜöýä▒ŕ│╝ ýťäÝŚśýŚÉ ŰîÇÝĽť ýőČŕ░üýä▒ýŁä ýŁŞýőŁýőťÝéČ ÝĽäýÜöýä▒ýŁä ýĽîŰáĄýú╝ýŚłŰőĄ. ŰśÉÝĽť ળýťÁ┬ĚŰ│┤ÝŚśýí░ýžüýŁś ÝŐ╣ýä▒ýâü ýáĽŰ│┤Ű│┤ ýĽłýŁä ýťäÝĽť ŕÁÉýťíý▓┤ŕ│äŕ░Ç ýל ýŁ┤ŰĄäýžÇŕ│á ý׳ýŁîýŚÉŰĆä ŰÂłŕÁČÝĽśŕ│á ýáĽŰ│┤Ű│┤ ýĽł ýťáýÂť ŕ┤ÇŰáĘ ýéČŕ│áŕ░Ç Ű╣łŰ▓łÝ׳ Ű░ťýâŁÝĽśŰŐö Ýśä ýőťýáÉýŚÉýäť ŕ░Çý׹ ý▓┤ŕ│ä ýáüýŁŞ ýáĽŰ│┤Ű│┤ýĽłýŁä ÝľëÝĽśŕ│á ý׳ŰŐö ýí░ýžüýŁś ŕÁČýä▒ýŤÉŰôĄýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ÝÖĽýŁŞÝĽśŰę┤ýäť ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁś ýáťŕ│á Űą╝ ŕ░ÇýáŞŰőĄýú╝ŕŞ░ ýťäÝĽť ýŚ░ŕÁČŰą╝ ýłśÝľëÝĽśýśÇŰőĄŰŐö ýáÉýŁ┤ŰőĄ.
Ű│Ş ýŚ░ŕÁČýŁś ÝĽťŕ│äýáÉŕ│╝ ÝľąÝŤä ýŚ░ŕÁČŰ░ęÝľąýŁÇ ŰőĄýŁîŕ│╝ ŕ░ÖŰőĄ. ý▓źýžŞ, ýí░ ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ŰÂäýäŁÝĽśŕŞ░ ýťäÝĽť ýÜö ýćîŰą╝ ýáĽýä▒ýáüýŁŞ ýŞíŰę┤ýť╝ŰíťŰžî ýáĹŕĚ╝ÝĽśýŚČ ŰÂäýäŁÝĽśýśÇŰőĄŰŐö ŕ▓âýŁ┤ŰőĄ. Ýľą ÝŤä ýőĄýžłýáüýŁŞ ŕŞ░ýŚůýŁś ýáĽŰčëýáüýŁŞ ýáĹŕĚ╝ýŁś Ű░ęýőŁýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ ýŚÉ ýśüÝľąýŁä Ű»Şý╣ť ýÜöýŁŞýŁä Ű╣äŕÁÉÝĽśŰę░ ŕŞ░ýŚůýŁś ý×ČŰČ┤ŰŹ░ýŁ┤Ýä░ ŕŞ░Ű░śýť╝Űíť ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ŰîÇÝĽť Ű╣äŕÁÉýÖÇ ŰÂäýäŁýŁ┤ ÝĽäýÜöÝĽá ŕ▓âýŁ┤ŰőĄ.
ŰĹśýžŞ, ŕ░ťýŁŞýŁś ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŁ┤ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýáĽý▒ůýĄÇýłśýŚÉ ýśüÝľąýŁä Ű»Şý╣śŰŐö ýÜöýŁŞýŁä ŕ▓ÇýáĽÝĽśŕŞ░ ýťäÝĽť ŕ░ÇýäĄýŁä ýłśŰŽŻÝĽť ŕ▓ŻŰíťýŚÉýäť ŕ░ťýŁŞýŁś ýŁŞýžÇýáü ý░ĘýŤÉýŁ┤ ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýä▒ŕ│╝ýŚÉ ýśüÝľąýŁä ŕ░ÇýáŞŰőĄ ýú╝ŰŐö ŕ▓âýť╝Űíť ÝîÉŰőĘÝĽśýśÇŰőĄ. ýÂöÝŤä ýŚ░ŕÁČýŚÉýäťŰŐö ýí░ýžüýŁś ýáĽŰ│┤Ű│┤ýĽłýἠý▒ůýĄÇýłśŕ░Ç ýí░ýžüŕÁČýä▒ýŤÉŰôĄýŁś ŕ░ťýŁŞýáü ý░ĘýŤÉýŁŞ ýáĽŰ│┤Ű│┤ýĽłýŁŞýőŁýŚÉŰĆä ýśüÝľąŰáąýŁä ŕ░ÇýáŞŰőĄýú╝ŰŐöýžÇ ÝÖĽýŁŞÝĽśŕŞ░ ýťäÝĽť ýŚ░ŕÁČŕ░ÇýäĄýŁä ýłśŰŽŻÝĽśýŚČ ŕ▓ÇýŽŁÝĽá ÝĽäýÜöýä▒ýŁ┤ ý׳ŰőĄ.
REFERENCES
1 Berejikian, J DÔÇťÔÇťA Cognitive Theory of DeterrenceÔÇŁÔÇŁ, Journal of Peace Research, (2002), Vol. 39, No. 2, pp. 165-183.

2 Bulgurcu, B, Cavusoglu, H and Benbasat, IÔÇťÔÇťInformation Security Policy Com- pliance: An Empirical Study of Rationality -Based Beliefs and Information Security AwarenessÔÇŁÔÇŁ, MIS Quarterly, (2010), Vol. 34, No. 3, pp. 523-548.

3 Chen, C C, Medlin, B D and Shaw, R SÔÇťÔÇťA Cross-Cultural Investigation of Situational Information Security Awareness ProgramsÔÇŁÔÇŁ, Information Management and Computer Security, (2008), Vol. 16, No. 4, pp. 360-376.

4 Choi, N, Kim, D, Goo, J and Whitmore, AÔÇťÔÇťKnowing is Doing: An Empirical Validation of theRelationship between Managerial Information Security Awareness and ActionÔÇŁÔÇŁ, Information Management and Computer Security, (2008), Vol. 16, No. 5, pp. 484-501.

5 Drevin, L, Kruger, H A and Steyn, TÔÇťÔÇťValue Focused Assessment of ICT Security Awareness in an Academic EnvironmentÔÇŁÔÇŁ, Computers and Security, (2007), Vol. 26, No. 1, pp. 36-43.

6 Frank, J, Shamir, B and Briggs, WÔÇťÔÇťSecurity-related Behavior of PC Users in OrganizationsÔÇŁÔÇŁ, Information and Management, (1991), Vol. 21, No. 3, pp. 127-135.

7 Goodhue, D L and Straub, D WÔÇťÔÇťSecurity Concerns of System User: A Study of Perceptions of the Adequacy of SecurityÔÇŁÔÇŁ, Information and Management, (1991), Vol. 20, No. 1, pp. 13-27.
8 Govindarajan, V and Fisher, JÔÇťÔÇťStrategy, Control Systems, and Resource Sharing: Effects on Business-unit PerformanceÔÇŁÔÇŁ, The Academy of Management Journal, (1990), Vol. 33, No. 2, pp. 259-285.

9 Ha, S W and Kim, H JÔÇťÔÇťThe Effects of UserÔÇÖs Security Awareness on Password Security BehaviorÔÇŁÔÇŁ, Journal of Digital Contents Society, (2013), Vol. 14, No. 2, pp. 179-189.

10 Kang, D Y and Chang, M HÔÇťÔÇťFactors Influencing on the Compliance of Information Security Policy of Workers of Shipping and Port OrganizationÔÇŁÔÇŁ, The Korea Port Economic Association, (2012), Vol. 28, No. 1, pp. 1-23.
11 Kang, J YÔÇťÔÇťA Study on the Systematized and Unified Plan of Port Logistics Security Management SystemÔÇŁÔÇŁ, Journal of Law and Politics research, (2013), Vol. 13, No. 2, pp. 389-436.
12 Kankanhalli, A, Teo, H H, Tan, B C Y and Wei, KÔÇťÔÇťAn Integrative Study of Information Systems Security EffectivenessÔÇŁÔÇŁ, International Journal of Information Management, (2003), Vol. 23, No. 2, pp. 139-154.

13 Kim, H j and Ahn, J HÔÇťÔÇťAn Empirical Study of EmployeeÔÇÖs Deviant Behavior for Improving Efficiency of Information Security GovernanceÔÇŁÔÇŁ, Society for e-Business Studies, (2013), Vol. 18, No. 1, pp. 147-164.

14 Kim, S H and Song, Y MÔÇťÔÇťAn Empirical Study on Motivational Factors Influencing Information Security Policy Compliance and Security Behavior of End-Users (Employees) in OrganizationsÔÇŁÔÇŁ, The e-Business Studies, (2011), Vol. 12, No. 3, pp. 327-249.

15 Knapp, K J, Marshall, T E, Rainer, R K and Ford, F NÔÇťManagerial Dimensions in Information Security: A Theoretical Model of Organizational Effectiveness White Paper, Information Systems Security Certification Consortium (ISC) 2005), 2.
16 Layton, TInformation Security Awareness, The Psychology behind the Technology, AuthorHouse 2005.
17 Lebow, R and Stein, JÔÇťÔÇťDeterrence: The Elusive Dependent VariableÔÇŁÔÇŁ, World Politics, (1990), Vol. 42, No. 3, pp. 336-369.

18 Lee, S M, Lee, S G and Yoo, SÔÇťÔÇťAn Integrative Model of Computer Abuse Based on Social Control and General Deterrence TheoriesÔÇŁÔÇŁ, Information and Management, (2004), Vol. 41, No. 6, pp. 707-718.

19 Lee, S J and Lee, M JÔÇťÔÇťAn Exploratory Study on the Information Security Culture IndicatorÔÇŁÔÇŁ, Informatization policy, (2008), Vol. 15, No. 3, pp. 100-119.
20 Nosworthy, JÔÇťÔÇťImplementing Information Security in the 21st Century-do You Have the Balancing Factors?ÔÇŁÔÇŁ, Computer and Security, (2000), Vol. 19, No. 4, pp. 337-347.

21 Park, C J and Yim, M SÔÇťÔÇťAn Understanding of Impact of Security Counter- measures on Persistent Policy ComplianceÔÇŁÔÇŁ, The Society of Digital Policy & Management, (2012), Vol. 10, No. 4, pp. 23-35.
22 Park, I B and Kim, J DÔÇťÔÇťA Study on the Policy Management for Industrial Security's CultureÔÇŁÔÇŁ, The Journal of Korean Association for Industry Security, (2011), Vol. 2, No. 1, pp. 33-46.
23 Park, J YÔÇťÔÇťAn Analysis on Training Curriculum for Educating Information Security ExpertsÔÇŁÔÇŁ, Management Information Systems Review, (2012), Vol. 31, No. 1, pp. 149-165.

24 Park, S SÔÇťÔÇťConcept of Strategy in Organizational Information SecurityÔÇŁÔÇŁ, Journal of Information and Security, (2007), Vol. 7, No. 3, pp. 15-24.
25 Rezgui, Y and Marks, AÔÇťÔÇťInformation Security Awareness in Higher Education: An Exploratory StudyÔÇŁÔÇŁ, Computers and Security, (2008), Vol. 27, No. 7-8, pp. 241-253.

26 Stanton, J, Stam, K, Mastrangelo, P and Jolton, JÔÇťÔÇťAnalysis of End User Security BehaviorsÔÇŁÔÇŁ, Computers and Security, (2005), Vol. 24, No. 2, pp. 124-133.

27 Siponen, M TÔÇťÔÇťA Conceptual Foundation for Organization Information Security AwarenessÔÇŁÔÇŁ, Information Management and Computer Security, (2000), Vol. 8, No. 1, pp. 31-41.
28 Siponen, M, Pahnila, S and Mahmood, M AÔÇťÔÇťCompliance with Information Security Policies: An Empirical InvestigationÔÇŁÔÇŁ, Computer, (2010), Vol. 43, No. 2, pp. 64-71.

29 Sun, H GÔÇťÔÇťImpacts of Information Security Policies and Organizations on the Information Security Performance in Korean EnterprisesÔÇŁÔÇŁ, The Korea Society of Management Information Systems proceedings, (2005), Vol. 2005, No. 1, pp. 1087-1095.
30 Woo, S HÔÇťÔÇťA Study on Security Capability of IDPSÔÇŁÔÇŁ, The Institute of Electronics and Information Engineers-CI, (2012), Vol. 49, No. 4, pp. 9-15.
31 Workman, M and Gathegi, JÔÇťÔÇťPuni- shment and Ethics Deterrents: A Study of Insider Security ContraventionÔÇŁÔÇŁ, Journal of the American Society for Information Science and Technolog, (2006), Vol. 58, No. 2, pp. 212-222.

32 Yim, M SÔÇťÔÇťA Path Way to Increase the Intention to Comply with Information Security Policy of EmployeesÔÇŁÔÇŁ, The Society of Digital Policy & Managemen, (2012), Vol. 10, No. 10, pp. 119-128.

 PDF Links
PDF Links PubReader
PubReader Full text via DOI
Full text via DOI Download Citation
Download Citation Print
Print




